Cyber Security Managed Services
Your comprehensive guide to services included,
budgeting, ROI, vendor evaluation, and more.
Cyber Security Managed Services
Your comprehensive guide to services included,
budgeting, ROI, vendor evaluation, and more.
Who’s taking care of your cybersecurity?
First published Nov 17, 2023. Updated March 13, 2024.
With cyber attacks growing 38% since 2022, and cyber security budgets growing 34.9% since 2020, companies of all sizes are scrambling to seal their defenses. They’re realizing that cyber security isn’t a “nice to have,” but a must-have—like loss prevention or legal protection.
Yet internal IT staff can’t take on cyber security. Between desktop support, phone, and network, they have their hands full.
Enter the cyber security managed services provider—also known as an MSSP (managed security services provider). This is a company that identifies, implements, and maintains cybersecurity controls—as well as consulting and providing strategic direction—under a managed services arrangement. Given the rapidly evolving threat landscape, companies are flocking to MSSPs to lock down their networks, users, data, and more.
But what’s included in these services? How do they interface with your IT department (or with IT managed services)? How do you find the right provider?
Hang on to your hats—we’ve got all the details below.
Contents
1. What are cyber security managed services?
“Cyber security managed services” refers to cybersecurity controls that are implemented, managed, and updated by a trusted partner. Given the difficulty of maintaining a team of cybersecurity experts on staff, outsourcing allows organizations to achieve the same level of security that an enterprise would.
Understanding the cybersecurity landscape
Cybercrime is growing rapidly. Global enterprises have hardened their defenses so well, cybercriminals are now turning to softer targets—which means businesses of all sizes.
- The cost of cybercrime is expected to grow 15% YoY for the next 3 years.*
- Cyberattacks rose 38% in 2022.*
- An estimated 54% of companies have experienced a cyberattack in the last 12 months.*
What does all this mean in financial terms?
The cost of a cyber incident varies, yet IBM reports that the average cost of a ransomware incident is $4.45M. This includes the ransom payment and any additional expenses incurred.
Clearly, every organization must define a cybersecurity strategy. And given budgetary limitations, a managed services model is far more effective in preventing devastating incidents.
Is cybersecurity different from IT managed services?
Great question!
Years ago, IT and cybersecurity were typically handled by different teams. In the world of managed services, this led to companies specializing in IT managed services, or cybersecurity—but not both. Some MSSPs still provide cybersecurity alone. They typically don’t remediate security incidents, but only report them.
(Hint: The best MSSPs do it all. Here at Corsica Technologies, we handle everything—IT managed services plus cyber security, with reporting and remediation.)
💡Want to learn more?
In today’s rapidly evolving threat landscape, it’s a risky proposition to separate IT from cyber. Simply put, every IT responsibility is also a cybersecurity responsibility. Consider a few examples.
- End user device management. Procuring, refreshing, and troubleshooting laptops is only part of the problem. What about MDM (mobile device management), which allows you to wipe a device remotely if it’s lost or stolen? For company-owned devices, this is a core component of cyber security managed services (see below, “What’s included in cyber security managed services?”).
- Network management. Monitoring, configuring, and replacing network hardware (like switches, firewalls, and wireless access points) is only part of the picture. What about MDR (managed detection and response)? This software comes with a team of specialists who monitor all aspects of your network and mitigate threats in real time.
- Email administration. It’s one thing to provision a new email address, whether on premises or in the cloud. But what about training new employees on the latest schemes in phishing emails? And when the unthinkable happens—when someone clicks a malicious link—who gets notified? Are they able to respond immediately, 24x7x365?
As you can see, cyber security really isn’t a separate discipline from IT. The two are deeply interwoven. This is why many organizations choose a provider who is both an MSP (managed services provider in IT) and an MSSP.
Basic, niche, and broad MSSPs
In the world of MSSPs, not all providers are created equal.
When it comes to depth of cyber security services, you’ll want to conduct due diligence and choose a partner who can cover your entire business with specialist expertise. (More on that below—“What to look for in cyber security managed services.”)
Broadly speaking, MSSP providers fall into three buckets.
Basic. The MSSP only covers foundational cybersecurity controls—things like automated patch management, data backups, and antivirus software. The MSSP may provide notifications only, with no remediation when an incident occurs.
Niche. The MSSP specializes in a particular branch of cyber security—maybe network security services, maybe end user security, maybe something else. While they have deep expertise in that discipline, they can’t help with your cybersecurity as a whole. And they certainly don’t integrate with your broader IT practice outside that niche.
Broad. The best MSSPs specialize in every single branch of cybersecurity. Their managed services include domain experts working on everything you need to mitigate risks to acceptable levels—across networks, devices, end users, email, and more. (Jump down to What’s Included to get the full picture.)
*Stat sources:
2. Cybersecurity maturity assessment
Every organization has a different maturity level when it comes to cybersecurity.
Perhaps you have a small IT staff, and you do the best you can in-house.
Maybe you have one person with cybersecurity experience—or no one.
Are your patches all up to date? What about your operating systems?
The key is to know where you stand today–and to take action to improve your security posture. Take our free assessment to see where you stand.
3. Why choose managed cybersecurity services?
First off, it’s important to understand the difference between an MSP and an MSSP.
An MSP (managed IT services provider) handles IT services such as infrastructure management, cloud system management, and so on.
An MSSP (managed cybersecurity services provider) handles all things cybersecurity.
Most organizations will get the best results working with a combined MSP/MSSP. Then you get one expert team handling cybersecurity and IT with an integrated approach.
💰FREE incident remediation?!
No joke. Just a few limitations.
The best MSSPs offer significant benefits that are difficult to achieve any other way. Here are the main drivers for choosing cyber security managed services.
A. You get proactive threat detection
Does your IT team have the tools to spot threats proactively? Even if they do, can they respond proactively? Or are they busy putting out fires with wireless access, crashing desktops, and server patches?
Cyber security really requires dedicated professionals. But those people don’t come cheap—and they’re difficult to keep on staff. Which leads us to another benefit of managed services.
B. You get affordable access to experts
It’s no secret that cybersecurity experts are expensive to hire in-house, earning an average of $120,000 per year.
Consider the fact that one expert isn’t enough. You’ll need a team of professionals to provide full coverage. CSO reports that “at the $100 million mark, most companies have between one and nine full-time security workers.”
Here’s a list of common cybersecurity titles and specializations. Note that a robust cybersecurity practice requires many of these roles—and this list isn’t exhaustive.
- Chief Information Security Officer (CISO)
- Cloud Security Architect
- Network Security Analyst
- Information Security Analyst
- Penetration Testing Specialist
- Intrusion Detection Analyst
- Threat Intelligence Analyst
- Cyber Insurance Policy Specialist
- Digital Forensics Analyst
- Government Compliance and Risk (GRC) Manager
- Cyber Incident Responder
For most organizations, it’s simply too expensive to hire (and keep) these experts on staff. They can earn a top salary anywhere they go. They tend to churn frequently due to stress and the abundance of opportunities available to them.
In contrast, managed services provide access to the right cyber security professionals at a highly affordable rate. Since cyber security becomes a line item with an SLA, rather than an in-house team, you get the certainty you need without the burden of internal management.
C. You get scalability and flexibility
Your network and IT needs are always changing. Your team may grow or shrink, which means a change in the number of end user devices connected to the network. You may enable remote workers—or bring people back to the office. New projects, lines of business, or partnerships may introduce changes in your IT needs.
Every time your IT needs change, your cyber security needs change. Change management for both IT and cybersecurity can be challenging to handle in-house. Software licenses, patches, hardware upgrades, regulatory compliance—this is one big, complex beast.
Managed cyber security services offer an advantage here too. You get an expert partner who handles your change management in regards to cyber security. Everything goes under one line item, and you know who to call when you have questions.
D. You get expert guidance on regulatory compliance
Do you know what regulations your organization must comply with? Do you know how they impact cybersecurity?
This is an area where managed cyber security services really stand out. A provider who works with many companies and industries maintains expert knowledge of all relevant regulations. Whether it’s HIPAA, CMMC, or an obscure regulation applying to your industry, an expert provider can explain what you need to do to achieve (or maintain) compliance. They can also implement the necessary cyber security controls.
E. You get a trusted partner handling your evolving complexity
Do you have the resources to stay on top of evolving cybersecurity trends? Most companies don’t unless they’re a multi-billion-dollar enterprise. For the rest of us, outsourcing to a trusted partner gives you a single line item, SLAs, and the knowledge that your MSSP has it covered.
F. You can move fast as threats evolve rapidly
The more resources you can put behind cyber security, the better. New threats are emerging all the time, and the pace of change has only increased since the pandemic. Managed cybersecurity services allow you to respond much faster than you could with limited in-house resources. You get access to an entire team of cyber experts who keep up with the latest threats as well as best practices.
E. You get a SOC (security operations center) without building it yourself
A SOC (security operations center) is the heart of any cyber security practice. It’s a team of experts who continuously monitor the organization’s networks, devices, and general IT infrastructure for cyber threats. When they detect a threat, they investigate and respond, minimizing damage.
A SOC is challenging to assemble (and maintain) in-house. Cybersecurity professionals are in high demand. When you outsource your SOC, you take a significant headache off the table.
F. Your IT team can focus on supporting the business
Let’s be honest, most IT teams have no time to work on cybersecurity. There’s simply too much going on. They spend all their time on reactive responses rather than proactive monitoring and mitigation.
Janet’s laptop just broke again, and she’s giving a big presentation today.
Wifi is down at the satellite office.
You’re behind on patches… again.
When you outsource cyber security, you get time back to focus on your core mission—supporting the business from a technology perspective. That’s a huge advantage, and a huge headache removed.
G. Protect revenue, customer relationships, and reputation… for less
Cybersecurity is essential to preventing downtime, data breaches, and damaged customer relationships. A cyber breach can tarnish your reputation and relationships, ultimately impacting revenue. While we hear about devastating cyber breaches in the news, we never hear about companies that prevented an attack.
Disaster avoided doesn’t always seem noteworthy, but consider the opposite. Bad press can spin out of control. Once your reputation is damaged, it’s almost impossible to recover it.
Outsourcing to an MSSP allows you to protect your assets without the cost and operational challenges of an in-house team. It’s a seamless way to get where you need to go in cybersecurity.
What types of companies typically use these services?
Multibillion-dollar global enterprises may have the resources to add top-tier professionals to their staff—and to manage these professionals as a cohesive team.
For the rest of us, in-house cybersecurity is often out of reach.
That said, even large enterprises get significant cost savings and reduction of headaches from outsourcing.
At the end of the day, organizations of all sizes, in all industries, gain cost savings and better security when they choose an expert service provider for cyber security. Here are some scenarios that we see most frequently.
- No IT or cybersecurity in house. These companies simply don’t have the resources to handle their technology needs. From managed network services to cyber security, they engage a trusted partner who covers both IT and cybersecurity.
- Some IT, but no cybersecurity in house. These organizations may have a small IT team, or even a single IT resource, who supports day-to-day operations. IT staff has no capacity to handle cybersecurity because they’re busy troubleshooting laptops or trying to fix the wireless network.
- Robust IT, limited cybersecurity in house. These companies are doing great things with their IT staff. They may have a team member or two with cybersecurity experience, but they don’t have the bandwidth to take a comprehensive approach.
What does this look like in real life?
Check out this customer video to see how Medpoint succeeds with managed cyber security services.
4. What’s included in cyber security managed services?
The best MSSPs will offer numerous managed cyber services that can be bundled in different ways. Things are most cost-effective (and most secure) when your MSSP is also your MSP—your managed services provider for IT.
With that in mind, here’s a list of the main services you should look for, broken up by category. Whether or not every service is a fit for you may depend on your current cybersecurity risk status, your budget, and the capabilities of your MSP/MSSP. Some services may be included in a bundle, while others may require an additional fee, depending on the provider’s policies.
A) Compliance Gap Assessments
How does your security posture stand up to applicable law? A compliance gap assessment measures your policies and processes against the relevant regulations at all levels of government, which can vary by state and industry. You get an easy-to-understand executive summary that tells you what’s wrong—and what you can do to fix it. (More on compliance gap assessments below.)
While a gap assessment is essential in regulated industries, it’s not the whole picture. You also need to assess your current risk. Which leads us to…
B) Cybersecurity Risk Assessments
Whether you’ve worked with an MSSP before, or this is your first time, you’ll want to kick off with a cybersecurity risk assessment—especially if it’s been more than a year since your last assessment. This is particularly important if you need cybersecurity insurance, as renewing this insurance often requires assessing cybersecurity risk on an annual basis. In a nutshell, this assessment is a clearly defined process in which cybersecurity experts audit your systems against a rubric for defining acceptable risk.
This might sound similar to a gap assessment like those associated with NIST 800-171 or ISO 27001:2013. While there are similarities, risk assessments have one big difference.
Gap assessments can make it seem like the organization must mitigate all risks completely. This is impossible due to 1) limited resources, and 2) the excessive friction it would introduce to business processes.
In contrast, a risk assessment defines (and allows) acceptable risk while providing sufficient security—all without introducing unnecessary friction to operations.
A cybersecurity risk assessment should be conducted every year. This ensures that your managed cyber security provider stays on top of your evolving landscape and any vulnerabilities that may arise. Learn more here: The Nuts and Bolts of Cybersecurity Risk Assessments.
C) Managed Security Services
- Managed Detection and Response (MDR). This service uses advanced software to detect threats on the network. The best MSSPs will provide human experts monitoring the software and responding to threats. MDR is the bedrock of managed cyber security services.
- Security Information and Event Management (SIEM). Pronounced “sim,” this is a software solution typically managed by your cybersecurity provider. It aggregates cybersecurity information in a single interface and empowers administrators to respond to security events. Without SIEM, it’s impossible to get all your essential security information in a single pane of glass in real time. Note that a managed SIEM provider should cover infrastructure, servers, and cloud software, like Microsoft 365.
- Security Alerting and Containment. Some MSSPs only offer alerting when a security event occurs. Others don’t stop with alerts—they actually contain the threat. Unless you have cybersecurity experts on staff, it’s essential to choose an MSSP who goes the extra mile and contains any threats detected.
- Dark Web Monitoring. Is your organization’s information for sale on the dark web? If so, how would you know until the unthinkable happens? Dark web monitoring by an expert cybersecurity partner can detect stolen information and provide a plan for mitigating the threat before it turns into a breach.
- Phish Testing and Security Awareness Training. Do your employees know how to spot a phishing email? Or are they ripe for the phishing? Criminals are getting more sophisticated than ever, impersonating executives, using urgent messages, and finding new ways to trick people. The best defense here is to stay on top of trends so you know what to look for. A cyber security services provider can train your employees and test their judgment in detecting phishing emails.
- Blocking Phish Emails. Microsoft 365 and Google Workspace aren’t perfect when it comes to cybersecurity. Threats like targeted spear phishing, social engineering, rogueware, scams, bank fraud and data exploitation can still evade the built-in controls in your email systems. Next-level protection ensures your employees can never click a dangerous link or download a harmful attachment.
- Browser Protection. Training is essential, but the most sophisticated browser attacks can trick even the best-educated employee. Browser protection blocks against social engineering scams, credential stealing, shareware, rogue software, and communication callbacks.
- Managed Patching (Windows and Third-Party). Every software solution and operating system needs patches from time to time. These updates help mitigate cybersecurity vulnerabilities that have been discovered in the code. Most organizations struggle to keep up with patching. A managed cyber security services company can implement automated solutions that ensure you’re always up to date.
D) Managed Network Security Services
- Managed Network Devices. Firewalls, switches, wireless access points, and even cloud networks all fall under managed network services. The right MSSP will protect your network in addition to everything else.
- Preventative Maintenance. Network security operations should never work in “reaction” mode only. Proactive maintenance is the best way to prevent outages and security incidents. This is why the best MSSPs don’t only respond to network alerts—they actually plan for the future, keep equipment up to date, and conduct maintenance before problems arise.
- Threat Hunting. You don’t know what you don’t know about your network. This is why the best MSSPs use sophisticated software and processes to detect potential threats in raw data coming from a network or system. Skilled experts analyze this data and identify potential threats to be investigated. Proactive threat hunting ensures your MSSP uncovers threats before the perpetrators can strike.
E) Managed Server Security Services
- Managed Servers. Does your team have bandwidth to keep up with server security? If not, an MSSP can help by keeping your servers on the latest OS with the latest patches.
- Backup and Disaster Recovery Services. Also known as DRaaS (disaster recovery as a service), this is a managed solution that makes copies of critical data and saves them for speedy restoration. It’s a core component of cyber security managed services. Depending on what your MSSP offers, this service may include assistance in developing your business continuity plan.
- Microsoft 365 and Active Directory Administration. Are M365 and Active Directory configured for maximum security? Is every user account current and locked down? Your MSSP can make sure everything is secure and up to date.
F) Managed End User Security Services
- Managed Workstations. If your workstation management isn’t centralized, then it’s incredibly difficult to keep every computer current and secure. The best MSSPs can assist with centralized workstation management.
- First Hour Application Support. Sometimes, your employees just need help with a new application on their machine. A combined MSP/MSSP should offer these services to keep your team working effectively.
- Workstation Repair/Reimage. A cybersecurity incident on an employee’s workstation may damage the device. In that case, your MSSP should be able to repair the device and return it to service.
G) Consulting Services and Deliverables
- Client Portal. The best MSSPs practice full transparency and self-service with their customers. For Corsica Technologies clients, this means an easy-to-use web interface that gives you the full picture on your managed cyber security and IT services. It covers everything from ticket management to your 3-year roadmap and more. Note that not every MSP/MSSP offers a client portal.
- Information Security Policy Library. Top MSSPs can provide a set of proven information security policy templates for building your own library. Your MSSP may also offer consulting to help establish this library (typically for an additional fee).
- Consulting from vCIO and/or vCISO. Not every organization can justify having an IT or cybersecurity executive on staff. This is where virtual CIO services offer a tremendous advantage. A virtual CIO (vCIO) is a fractional executive who consults on all things cybersecurity and IT. When you work with a combined MSP/MSSP, you can also get expert cybersecurity consulting in lieu of having your own CISO (chief information security officer). It’s a great value for organizations that need enterprise-class security but can’t justify the expense of staff hires.
- 3-Year Technology & Cyber Security Roadmap. If your spending in IT and cybersecurity feels like a rollercoaster ride, then something is broken. Most likely, you’re missing that 50,000-foot perspective and proactive strategy. A best MSP/MSSPs should help you craft a 3-year roadmap for technology and cyber security services. This is a living document that defines where you’re at today, where you need to go, and how you’ll get there in terms of technology investments. It’s essential to ditching the rollercoaster and achieving predictable, manageable spending in IT and cyber security.
- Strategic AI Consulting. Believe it or not, AI solutions like ChatGPT can pose a cybersecurity risk. Organizations need to understand the risks and define AI policies that allow them to leverage the power of AI without exposing sensitive data. This is why the best MSSPs offer strategic AI consulting services.
H) Advanced Cyber Security Services
- Internal Vulnerability Scanning. How secure are you from an insider threat? If a malicious actor already has legitimate access to some systems, how easy is it for them to exploit those internal vulnerabilities? This type of scanning answers these questions and provides steps for remediation.
- External Vulnerability Scanning. How easy is it to breach your network from the outside? External vulnerability scanning hunts for these weaknesses and provides a plan for remediation.
- Endpoint Vulnerability Scanning. Endpoints (remote devices connected to a network) can present vulnerabilities when an operating system or application has an unknown weakness. In some cases, the vulnerability may be well-documented, but the operating system or application hasn’t been upgraded to the latest version. Endpoint vulnerability scanning detects these issues and provides a plan for remediation.
Do these managed services include cyber security insurance?
MSSPs typically don’t provide cyber security insurance. This is a separate product coming from a separate industry. However, your MSSP should be able to provide a warm handoff to a recommended cybersecurity insurer.
If your MSSP doesn’t have a recommendation, check out Cysurance. This next-generation risk mitigation company insures, warrants, and certifies security solutions deployed by enterprise end-users.
Hint: Corsica Technologies is a Cysurance-certified provider of cyber security services. In fact, this relationship allows us to offer the Corsica Secure Service Guarantee, which covers certain financial losses for our clients in the event of a cybersecurity incident. Reach out to us to learn more.
Want to make sure you qualify for cybersecurity insurance? Start your journey here: Cybersecurity Insurance Requirements: 9 Controls You’ll Need.
5. How much should you budget for cyber security managed services?
According to IANS, the average portion of the IT budget allocated to cybersecurity has grown 34.9% since 2020—from 8.6% to 11.6%.
That’s for companies of all sizes. When you look at IANS’ information for organizations with <$100M in annual revenue, the allocations look quite different.
- IANS found that 18% of IT budget goes to cybersecurity.
- IANS found that a typical cybersecurity budget is 2.78% of annual revenue.
Using IANS’ data, that means a typical $100M company can be expected to budget $2.78M for cybersecurity.
Even a smaller organization at $10M could be expected to set aside $278,000 for cybersecurity.
If that seems like a lot, consider the cost of a breach.
- IBM reports that the average data breach costs $4.45M worldwide—and $9.48M in the US.
- Pingdom reports the average cost of a 1-hour outage in various industries:
- Auto industry – $3M/hour
- Manufacturing – $260k/hour
- Media – $90k/hour
- Healthcare – $636k/hour
- Retail – $1.1M/hour
- Telecom – $2M/hour
- Energy – $2.48M/hour
Clearly, the cost of a cybersecurity incident can be catastrophic. How do you know if you’re controlling cybersecurity spending appropriately while also mitigating risk effectively?
Welcome to our next topic, cybersecurity ROSI. Let’s unpack that.
6. How do you calculate cybersecurity ROI/ROSI?
It’s essential to quantify the value of cybersecurity investments. But doing so can be quite difficult.
For one thing, traditional ROI isn’t the right concept (or calculation) to quantify the value of cybersecurity investments. ROI is about revenue that can be attributed to an investment. For example, a marketing campaign might have a specific cost, and marketers may be able to attribute specific leads (and customers) to this campaign. An ROI calculation is possible because the investment was designed to drive revenue, and a proportion of revenue can be tied back to the campaign.
Yet cybersecurity isn’t a revenue-driving endeavor. Telling customers about your security investments will give them greater faith in your company, and it will increase your brand equity, but it won’t drive new business.
This is why you should evaluate cyber security managed services in terms of ROSI—return on security investment. This formula looks quite a bit different from ROI.
ROSI = ([ALE x mitigation ratio] – cost of solution) / cost of solution
See how the formula works with our FREE calculator below.
There’s a lot to know about this formula, particularly the variables labeled “ALE” and “mitigation ratio.” ALE refers to “annualized loss expectancy” in dollars, while the mitigation ratio expresses the effectiveness of the solution in stopping all attacks that it addresses.
Check out this in-depth article to learn more: Calculating Cybersecurity ROI/ROSI.
Bottom line, it’s essential to calculate the return from a cybersecurity investment in the right financial terms.
It may be challenging for other stakeholders to move away from an ROI calculation, but once you explain how ROSI works (and show the numbers), it should become clear how valuable your cybersecurity investment realy is.
7. Can MSSPs help with regulatory compliance and other risks?
Absolutely! Regulatory compliance is an essential part of managed cyber security services. Your provider should be familiar with the regulation that applies to your company—and what it means for cybersecurity.
The first step in achieving regulatory compliance is a gap assessment, also known as a gap analysis.
The assessment process audits your organization’s processes and policies and compares them to the applicable regulations at the local, state, and federal level. The deliverable is an executive summary that outlines your standing—and steps for mitigation—in plain language.
Here are a few types of gap assessments typically covered by an MSSP:
- CMMC (Cybersecurity Maturity Model Certification)
- PCI-DSS (Payment Card Industry Data Security Standard)
- HIPAA (Health Insurance Portability and Accountability Act)
- CJIS (Criminal Justice Information Services)
If your organization falls under one of these regulatory frameworks, and you haven’t done a gap assessment in a while, it’s essential to find out where you stand.
Can MSSPs advise on the use of generative AI like ChatGPT?
Generative AI is so new, there are still a lot of unknowns. The field is still evolving, which means the impact of AI on cybersecurity is still evolving.
Believe it or not, generative AI like ChatGPT can pose a cybersecurity risk.
This is why the best MSSPs can help you define company policies regarding generative AI.
For Microsoft customers, we actually recommend Microsoft Copilot over ChatGPT. Copilot allows organizations to leverage the productivity of generative AI while avoiding the significant downsides of ChatGPT.
What’s the story here?
In a nutshell, Microsoft Copilot and ChatGPT appear superficially similar. Both are LLMs (large language models). They take written prompts, interpret them in light of statistical models, and produce text based on statistical modeling. But that’s where the similarity ends. Here’s what you need to know at a high level:
ChatGPT has no access to your internal company data, while Copilot is deeply integrated into your Microsoft 365 environment.
Copilot actually functions like a member of your team. It can work with your proprietary data and produce outputs that are contextualized to your operations.
Information entered in a ChatGPT prompt can leak out in ChatGPT outputs—because OpenAI uses text prompts to continue training the AI. This is a significant cybersecurity risk.
Microsoft Copilot does not use prompts to train the AI. Microsoft does not repurpose user-generated prompts for AI training. They deeply respect customers’ data privacy.
Read more here: Microsoft Copilot vs. ChatGPT.
8. What to look for in cyber security managed service provider
Unfortunately, not all MSSPs are created equal. It’s important to educate yourself as you assess vendors so you can vet them properly.
So how do you evaluate and hire the best MSSP for your organization?
Here are some essential characteristics of a top-notch MSSP.
Industry experience
How long has the provider been in business? While cyber security managed services are always evolving, you want a company with a long tenure and a deep bench. The more collective experience your MSSP has, the better.
Reputation and reviews
What do other customers think of the company? Check out their reviews on Google, G2, and other sites. Read a wide sample of reviews, from 1-star to 5-star. No company is perfect, but a slice of life as experienced by other customers can help you understand an MSSP’s strengths and weaknesses.
Comprehensive, flexible service offerings
Some MSSPs specialize in certain managed services. The best providers cover every type of cyber security service. You’ll want to make sure your provider offers the services you need. However, consider the fact that a non-comprehensive provider doesn’t have much incentive to alert you to services you don’t know you need.
For this reason, it’s usually best to look for a provider who does it all. Since cyber security intersects with IT managed services, you’ll want to consider a combined MSP/MSSP as well.
Hint: That’s what we’re all about here at Corsica Technologies.
Can actually remediate security incidents
Believe it or not, some MSSPs don’t remediate security incidents. Rather, they only notify you when there’s an issue.
Then it’s your problem to fix it.
Here at Corsica Technologies, we believe no one should have to remediate their own cyber security incidents. You have enough on your plate with existing IT tasks, so why not engage a trusted partner who not only notifies you, but remediates issues?
Fits your budget
Cyber security managed services have to work for your budget. You’ll want to make sure your provider knows how to make cyber security work for you.
That said, you’ll also want to become familiar with recommended budget proportions for cybersecurity. As we noted above, organizations with <$100M in annual revenue should typically budget 2.78% of annual revenue for cyber security.
Security certifications
Managed services aren’t much good if your provider doesn’t have cyber security certifications.
But which certifications matter most? Here are some of the most important ones to look for.



This is only the tip of the iceberg. Check out all of Corsica Technologies’ cybersecurity certifications.
Equipped to move you toward Zero Trust
Zero Trust Architecture (ZTA) is critical for legacy organizations as the cyberthreat landscape continues to evolve. In a nutshell, Zero Trust is an approach that makes it difficult for a hostile actor to move within a network or system once they gain access. The model has four maturity stages and requires continual evolution. Since it’s difficult to manage in-house, it’s a key component of cyber security managed services.
Learn more here: Zero Trust for Small Businesses.
Covers cyber security and IT managed services
Some companies claim to be a combined MSP/MSSP, but they actually outsource the cyber security component.
When an incident occurs, the third-party MSSP notifies the MSP—and does nothing else.
This is not a good arrangement. You want a true combined MSP/MSSP—one who doesn’t outsource cyber security. This ensures that your provider’s teams work closely together, offering a holistic approach to cyber security and IT managed services.
Virtual CIO/CISO
If you don’t have a C-level executive in IT or cyber security, your managed services provider should be able to provide one. A virtual CIO/CISO provides C-level insight, consulting, strategy, and direction under a fractional-time model. This gives you the power of deep professional experience without the expense of keeping this person on staff. Learn more here: Virtual CIO Services.
Fills your gaps in IT staffing
Some MSP/MSSPs want to take over all IT operations—even if it means pushing out existing IT staff.
If you find a company like this, run for the hills!
The best MSP/MSSPs are flexible enough to fill your gaps without trying to take over. The relationship has to work for your organization and your team first. The right provider will recognize this from the very start.
Fits your availability requirements
How often do you want to check in with your MSSP? What response times do you need for phone calls, emails, and tickets? Make sure you ask tough questions and get the answers you’re looking for.
9. How to get started with cyber security managed services
Cyber security can be daunting—and the thought of evaluating managed service providers doesn’t make it any easier.
However, with the right plan, you can easily evaluate providers and choose the right one for your organization.
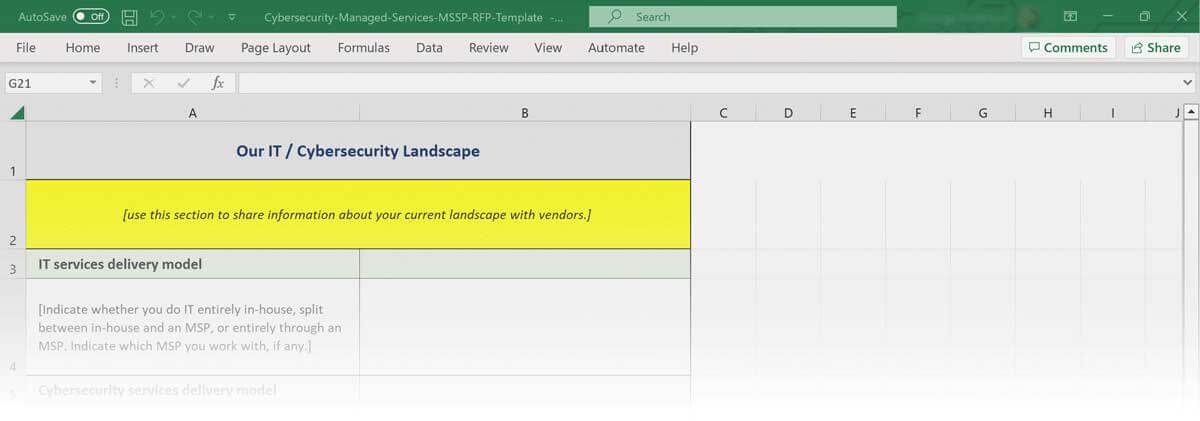
It all starts with a cyber security services RFP. Putting your requirements down on paper (or typing them up in Excel) specifies exactly what you’re looking for. It also gives you a framework for evaluating potential service providers.
Get started with our FREE Cyber Security Services RFP Template.
Once you’ve chosen your MSSP, the fun part begins.
If you’re in a regulated industry, your MSSP will probably want to start with a compliance gap assessment. This exercise compares your existing processes, technology, and policies with applicable regulation. It provides a path forward in cyber security as you start to work with a managed services provider.
Whether you’re in a regulated industry or not, a cybersecurity risk assessment also helps establish the path you’ll take to achieve greater security. Your MSSP may recommend this process as well.
10. Expert tips for cybersecurity management
You can start improving your cybersecurity management before you sign up with an MSSP. Here’s some low-hanging fruit that you can start implementing today. You won’t get nearly as much security as a managed provider offers, but every little bit helps as you start exploring your options with MSSPs.
Here are some things you can do today to start managing cybersecurity better.
- Enforce strong password policies
- Add multi-factor authentication
- Configure desktops to lock after 10 minutes of inactivity
- Provide phishing training and educate your staff on phishing techniques
- Add keypad security for physical office entry
- Check all network gear and workstations for up-to-date patching
Once you’ve done these things, you can rest well knowing you’ve added some additional security before you approach an MSSP. This list isn’t foolproof, and a managed services provider will take you much farther in cyber security—but it’s great to start with the easy stuff.
The final word
At the end of the day, cyber security is getting too complex (and risky) for organizations to handle in-house. With cybercrime rising 38% since 2022 and cybersecurity professionals earning top dollar, many organizations are struggling to lock down their networks, data, and devices.
The best MSSPs solve this problem with solid strategy, implementation, and support from top-tier professionals in cybersecurity. Since they offer all this for less than the cost of an in-house team, they’re a great choice for companies that don’t have the resources to handle cybersecurity themselves.