What are IT solutions for the manufacturing industry?
IT solutions for the manufacturing industry are any type of software or IT service intended to support a manufacturing environment. These solutions typically emphasize reliability, security, compliance, and performance. These solutions include managed IT services, network infrastructure, cloud platforms, cybersecurity, data backup, and application support tailored to the unique demands of manufacturing operations.
Unlike traditional office IT, manufacturing IT must account for shop-floor systems, industrial equipment, and operational technology (OT). The goal is to ensure technology enables efficient production, protects intellectual property, and supports business continuity without disrupting operations.
How do IT solutions support manufacturing plants and multiple facilities?
IT solutions connect manufacturing plants, warehouses, and corporate offices through centralized networks and shared systems. Secure connectivity allows production data, design files, and enterprise applications such as ERP or MES to remain synchronized across locations.
Centralized monitoring and management enable IT teams to maintain consistent performance and security standards at every facility. This approach reduces complexity, improves visibility, and allows manufacturers to manage multi-site operations as a unified environment.
Why is uptime so important in manufacturing IT environments?
Uptime is critical in manufacturing because even brief system outages can halt production lines, delay shipments, and cause significant financial losses. Manufacturing schedules often run continuously, leaving little margin for unplanned downtime.
Proactive IT monitoring, maintenance, and redundancy help identify issues before they escalate into outages. Reliable uptime ensures production targets are met, supply chains remain intact, and customer commitments are fulfilled.
Can IT services support automation and smart manufacturing systems?
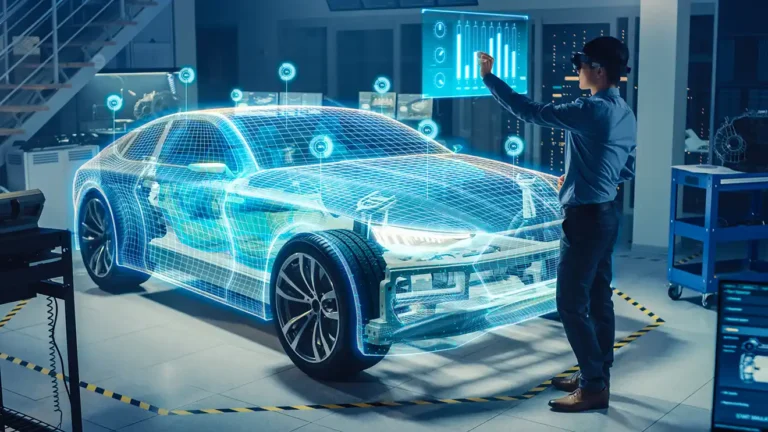
Yes, IT services play a foundational role in supporting automation and smart manufacturing systems. Modern production environments rely on connected machines, sensors, and software platforms to collect and analyze real-time data.
IT services help integrate automation systems securely, maintain network performance, and ensure data flows reliably between machines, control systems, and business applications. This support enables manufacturers to improve efficiency, visibility, and decision-making.
How does cybersecurity protect manufacturing operations?
Cybersecurity protects manufacturing operations by safeguarding production systems, intellectual property, and sensitive business data from cyber threats. Manufacturing environments are increasingly targeted due to their reliance on connected systems and the potential impact of downtime.
Note that OT (operational technology) comes with unique cybersecurity requirements. These tools often lack the computational resources to run endpoint security agents, which means they require passive, agentless monitoring. Microsoft Defender for IoT is one of the best tools on the market to protect OT equipment.
Across OT and IT equipment, effective cybersecurity measures include network segmentation, access controls, continuous monitoring, and employee awareness training. These protections help prevent disruptions, protect operational continuity, and reduce the risk of costly incidents.
What role does IT procurement play for manufacturers?
IT procurement ensures manufacturers acquire reliable, compatible, and cost-effective technology that supports both current operations and future growth. This includes hardware, software, licenses, and industrial-compatible systems.
Strategic procurement helps avoid mismatched technology, reduces lifecycle costs, and ensures equipment meets performance, security, and compliance requirements. Proper procurement also streamlines vendor management and technology standardization.
How do IT solutions scale as manufacturing operations grow?
Scalable IT solutions allow manufacturers to expand production, add facilities, or increase automation without rebuilding their technology foundation. Cloud services, modular infrastructure, and flexible support models make it easier to adapt as needs change.
As operations grow, IT solutions can be adjusted to handle higher data volumes, additional users, and new systems while maintaining performance and security. This scalability supports long-term business growth without unnecessary disruption.
How do IT solutions allow manufacturers to focus on production?
By managing and maintaining technology behind the scenes, IT solutions free manufacturers from day-to-day technical issues. Proactive support reduces disruptions and ensures systems operate reliably.
Some manufacturers choose to outsource their IT services entirely, an arrangement known as fully managed services. Others may bring in an MSP (managed service provider) to fill gaps in their team’s capabilities, shift coverage, or strategic perspective. This arrangement is known as co-managed services.
Whether fully managed or co-managed, outsourced IT capabilities allow internal teams to focus on their core responsibilities. This alignment allows technology to support manufacturing goals rather than distract from them.