
Copilot vs. ChatGPT for Business: UPDATED 2026
💡 Compare Copilot vs. ChatGPT Get Your FREE Chart Originally published November 1, 2023. Completely refreshed March 31, 2026. Short answers: ChatGPT is better for
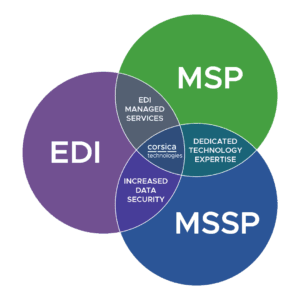
You get a single team handling cybersecurity, IT, and data integration services like EDI, filling the gaps in your team.
“Corsica is a one-stop shop for us. If I have a problem, I can go to my vCIO or a number of people, and you take care of it. That’s an investment in mutual success.”
– Greg Sopcak | Southern Michigan Bank & Trust
From 24/7 SOC services to MDR/SIEM, penetration testing and training, we’ve got you covered.
Get the expert support you need for your network, on-premises devices, VoiP, M365, Google Workplace, and everything in between.
Full support of compliance frameworks, including CJIS, HIPAA, CMMC, NIST, SOC 2, and more
Cut through the hype with smart strategies and right-fit AI solutions for your organization.
Take strategic steps with confidence as you collaborate with our expert business and vCIO consultants.
Get cloud security, integration, server virtualization, and optimization strategies to reduce your cloud costs.
Connect any data source to any other with robust solutions and managed services.
Stay ahead of the curve, eliminate waste, and grow revenue with next-generation technologies.
Expert consulting, implementation, integration, managed services, and cybersecurity for Microsoft products.
One program. One partner. Complete AI transformation.
It takes dedicated experience to use technology strategically in your industry. That’s why we specialize in certain verticals while offering comprehensive technology services.
From webinars and video tutorials to guides and blogs, we’ve got resources to help you and your team address any technology challenge.
Once you’ve detected a cybersecurity attack, it’s essential to respond fast. That’s why we monitor your systems 24/7/365, working quickly to contain and eradicate threats.


It’s tough to keep up without dedicated resources.
Get the comprehensive cybersecurity team you need for roughly the cost of ONE staff hire. Our team handles monitoring, threat detection, remediation, and more, while you focus on your core business.
Get the security operations center you need with a team that works 24/7/365. Our SOC never sleeps as we protect your data, systems, customers, and internal users from emerging cyber threats.
Are you backing things up as you should? Get peace of mind knowing your data is secure. Our solutions cover two essential components—data backup PLUS disaster recovery plans and processes.
If you can’t detect a cyberattack, you can’t even respond. Managed detection and response gives you the technology, the people, and the monitoring processes to lock down cyberattacks.
Who’s checking your patches? Do they have the time and energy for this essential function? Let our team manage your patching (Windows and third party) so you can focus on your core business.
Are you easy to hack? How would you even know before the unthinkable happens? Penetration testing puts your systems through a rigorous evaluation. You get actionable steps to improve security.
People will always be the weakest link in cybersecurity. Make sure your team is informed, tested, and up-to-date on the latest threats like spear phishing, whaling, cross-site scripting attacks, and more.
It’s impossible to eliminate risk. But what if you could quantify it—PLUS define a threshold of acceptable risk and take action to improve? It all starts with a cybersecurity risk assessment from our team.

In today’s cyberthreat landscape, businesses must maintain cyber readiness to defend their systems against ransomware, email compromise, and other advanced security threats.
Our full-scale services detect and close down threat actors quickly. We’re so confident in our abilities, we offer FREE incident remediation services, with limitations. See our Cybersecurity Service Guarantee for more.
Watch to learn more about what a SOC is and the role it plays in keeping businesses up and running. A Security Operations Center is the reporting point for a lot of different toolsets. A firewall or antivirus is no longer enough to protect your business. Advanced monitoring toolsets and techniques are required to detect and remediate cybersecurity threats.
Fill out this form, and we’ll respond within one business day. Let’s explore how we can support your business with robust cybersecurity services.
So it still takes the expertise Yep. To tune the systems, watch the systems respond, and then a broader expertise to to follow that instant response plan and involve the right people along the way. We're not editing that, by the way. We had to already start over once. Alright. So we're here to talk about events. Yes. Which often are alerts. They can be alerts. They can they can create alerts. Correct. So and, incidents and and specifically how they relate to security, but but you've dealt with events for a long time or the IT side of it. I dealt with events that were IT related. So, you know, events and, incidents are two different things. An event is something that could become an incident, and an incident is something that's actively happening that, you know, at least in the IT world, whether bring your systems down or or hugely impact your ability to do business So, one example would be, like, performance indicators and a an an alert that comes across as a performance indicator across mall I'm gonna geek out a little bit multiple, virtual machines that are on the same data store. But when you really dig into it, you find that it a controller that has like a, like, bad cash on and on the host itself. Like, that would be, that would suddenly move it from an event into an incident. That that needs to be corrected immediately, you know, because that's impacting everything. Yeah. So it's safe to say an incident could be caused by one or more events. Correct. And the incident is when you have the the impactual is that a word? Impactual. I don't. I do not think that that's a word. I think it's a word. So so what I'm hearing is you are better at knee jerk conversations than you are when you have to retread the same ground. This is interesting. I'm getting to know more about you. It's good. I'm I'm used to having AI. Right things for me now. So it's it's to come up with them off the top of my head. So so those are are when the business actually experience an impact, right, from one or more events Correct. And and the true the the same is true for security as well. We use that same framework or same way of thinking about events and and instance. Why? I mean, why don't we just respond to every event that happens? Whether it's IT or Because we'd be running around like chickens with cut off, and we would we would likely muddy the waters. So you have to, you have to really look into, you know, one, it's not one size fits all. Some of it is, but not all of it. Some of it's, you know, definitely cater to your business. And then one example I can think of is, you know, out of the country, alerts that would be events for, like, people who are maybe in Egypt logging in. Well, they might have a very good reason. Somebody might actually be in Egypt logging in. And if you were treating every one of those as an event, I mean, sorry, as a, as an instant, I mean, you would that's all you would do all day long. So you have to have some checks and balances in place. You have to have people who understand, understand the the tool set, right, and can easily you know, tune it to tune out any of the white noise that would happen and really dig and really, you know, identify what are, instance versus what are just, like, events that can be easily looked through very quickly and going, okay, just a couple pieces of corroborate, corroborating evidence, and we understand that that's likely an actual, incident. Okay. Yeah. That that makes sense. So You're responding. You're like, Okay. Okay. Well, it was kind of a long response. Well, it was a long question. It was short question. I think it was pretty long. So we'll play it back. So so if if we think about, you know, in terms of security posture and and what matters, we don't wanna we don't wanna respond to every event. Do wanna capture them all. Right. And then how do we figure out which ones are becoming incidents? Or at what point do we know when happens. Yeah. So, I mean, the enrichment of data from other, apps, or different, different reporting technologies can be brought in to a seam SIM. Either one is correct. Depending on who you talk. I hate you. Okay. So, and Microsoft actually provides a a really good, SIM application that is backed by AI. And if you haven't watched the video, we did make a video on AI. That can help identify programmatically, what could possibly really be incidents. And it's not it's not bad. It's pretty good. So so, you you know, another way to think about this is the more events you have the better you're gonna understand your incidents because you have more data points to back up what's happening. And once we determine an incident is occurring, there there's something we do different than an event. Right. We're we're likely, you know, engaging teams to start analyzing what's happening, lock it down, and then gain some perspective and start remediating. Okay. And that's done through a a process. Yes. That's done through a process and procedure. I just can't remember the name of it. Instant response, please. Thank you. I can't. I couldn't. I honestly couldn't remember it. Let's just keep going. So so as as we look at the way IT departments deal with incidents, we see a lot of variation, a lot of inconsistent see across the board. We see people that, you know, spend way too much time on on the events that are happening not enough time on incidents. We see people that turn every event into an incident. And our like you said, you know, you're running around. We we see people with emergency for emergency. We see people who think they're covered to get them back up by their insurance provider, but that's not what their insurance provider is there to do. With their forensics teams. Like, it's just, you know, misplaced, understanding of what's what's really happening and what you purchased. Like, so it's it's across the board. It's it's different. And really the way we do it here is we have a a combined team of administrators and secure of IT administrators and security analysts. One set is really working towards figuring out where, something's happening and can maintaining it. The other one the other side's figuring out how to, you know, maintain, like, keep you running as a business, or if you are down, bringing you back up as fast as pop So you can ship whatever widget you need out of your shipping department, right, like getting your trucks moving. Right. So that's the way that we found is the, is the best solution to this problem. And it and it's always evolving. It's always evolving. So so Yeah. That that makes a lot of sense. What what do you see when you work with a new company that maybe has some of the tools in place, but is spending a lot of time chasing events or has a lot of events, but not a good incident response plan. What are the, like, what does that lead to? It's training of resources. I mean, I don't think, I don't think when, leadership really, really sits down. They understand what it what having a cybersecurity team or having some cybersecurity awareness really looks like day to day. I mean, you know, you have to staff to have people kind of aware about what's going on. Twenty four seven three sixty five. We don't see a lot of these, incidents happen, while everybody's awake. Right. You know? And while while people are able to jump on it, Ealey. Yeah. One of one of my favorite examples of that is, I got a call Easter Sunday morning. I yeah. And, you know, it it was not for a customer, but it was for a a business that we had been talking to you about working with us, and that event started the night before. So, you know, the those events led to an incident but were not detected until that instant was was well down the road to BNA. Really, you know, having a big impact on the business. And this customer had a firewall sorry. This prospect had a firewall. They had some applications that were security minded. They had alerts. They actually had an MSSP in place. That that only I forgotten that part. Only alerted, but didn't take any action. Right. And I think that's, you know, one of the things that that I tell people when when talking to them about this is, you know, all the tools you can monitor everything. It's like a security system in your home. Mhmm. You're gonna have it all there if you don't ever arm it, when you leave, you're never gonna know when somebody breaks in right till you get back. And and you could look back and say, oh, man. Me open my door while I was gone Mhmm. And see the that event, but but you don't know or you can't take action that actually could prevent the impact of of those And we, and at one point in time, we we operated out of that paradigm too. It was a while ago, but we had like the separate cyber solution that would, you know, just basically throw, throw the alerts and everything for remediation over the fence. I mean, that was quite a while ago. But That's true. But it's a common way of of operating issues. Yeah. We have this security team. All they do is watch for these So when they happen, they say, Hey, IT team, you need to fix this. Right. And that's that's a breakdown point. When can't afford a breakdown. The last the last thing we need is a mishandling of of what's the the start of a security incident that we likely could shut down very quickly. No one's gonna care, you know, when they get breached that they didn't buy our cyber security offering that, you know, our name is right alongside theirs in the newspaper. So Yeah. Yeah. It makes complete sense to have, to have teams that are, that are integrated, you know, that that can respond with a with a full gamut of IT and and cyber security knowledge. And I think we we do that pretty well. Yeah. Yeah. I I we do, but most businesses don't have the resource to have somebody watching twenty four seven, somebody available to respond. Yeah. It's multiple somebody's, right? Right. It's multiple somebody. So now you're talking about expanding, expanding the amount of employees you have, you know, giving them benefits. It it's it's quite a task. And You can the other thing that we see often is, well, if I just buy X, well, so you bought X. Now you have to configure X that that watches whatever you need it to watch. And then you have to, administrate X, right? And then you have to the maintenance on it to keep it up to keep it, like, up signatures up to date and and alerting up to date and all that stuff. Like, that all takes, human, human capital. That's what it takes. And I think the the cool thing is that we, we've bought that human capital. We have that human capital. And we can easily deploy it to, you know, prospects almost anywhere in the world. Yeah. The, the easiest part of this is buying the tools. Yeah. The hardest part is making those tools really work for you and and protect you. And I know we've gone into multiple environments that had tools but the alerts were shut off. Yeah. They they're mothballed, essentially. And and I and I get it why their IT administrators did that, right? Because it's like I I can either help Brenda get her printer back online so she can, you know, print out checks for people, you know, payroll and stuff like that, or I can deal with four hundred alerts, I don't really understand might, and most of them might just be white noise. And they're all it takes to that one that's really not. And I and even, was Equifax, or who was the, who's the, the credit card company that, that had the, the breach. And it was one, like, alert Yeah. That had fired like six months or three months prior to that. I'm sorry, I I don't remember which one it is, but it was a major one. And they just had thought that was white noise. Yeah. You know, I can I can completely understand? This is not on any of those guys. So it still takes the expertise Yep. To tune the systems, watch the systems respond, and then a broader expertise to to follow that instant response plan and involve the right people along the way. One of the most frustrating, instance that that I was a part of, the executive team, the leadership team, didn't find out until things were way, way too far gone. So decisions that that they should have been involved in, they weren't involved in. And so having that in response plan, knowing what happens is these events turn into an incident and knowing when to involve the rest of your company is a is a key part of that as well. And something that that either you have to invest the time for or you use a provider like Corsica that they can do they can do that for you. Yeah. Everybody has to be kind of on board from the top down. It can't be driven by IT. Yeah. So security is a it's a business issue. It's not a technology issue. Right? Okay. Well, well, Nate, this has been this has been great. For spending some time. Yeah. No problem. I enjoy this time. I do to you. And and
What processes and roles should you establish BEFORE an incident occurs? What does the incident response process look like? Here’s everything you need to know.
But the best response process in the world won’t help if your organization isn’t prepared before an incident occurs.
In this article, we’ll cover everything you need to establish before an incident.
Then we’ll cover the actual process of incident response and containment.

Your SOC is the lifeblood of your cybersecurity operations. Without a SOC and the experienced professionals and technology that accompany it, it’s nearly impossible to respond to an incident—let alone contain it.
Here’s what a brief overview of what a SOC gives you.
Midmarket organizations typically can’t handle all this on their own. Existing IT staff can’t cover the additional workload of cybersecurity—and they don’t often have the experience to do so. Hiring dedicated cybersecurity professionals is difficult due to high salary expectations and frequent churn.
For these reasons, midmarket organizations often outsource this function to a cybersecurity managed services provider.
When a cybersecurity incident occurs, one of the first things your analysts will do is try to contain the threat. To achieve this, they need full documentation of your network. This includes things like:
You should have this documentation in place anyway, but the key here is to keep it up to date. You want to be prepared when an incident occurs.
No network, device, or cloud system is immune to catastrophe. A cybersecurity incident can result in data loss or corruption, making backup and recovery an essential function to establish before an incident occurs.
Due to the expense and skilled labor required, many midmarket organizations outsource this function to an MSSP (managed security services provider). Learn more here: Backup And Disaster Recovery Services.

This might sound similar to backup and disaster recovery, but it’s actually quite different.
Backup and disaster recovery is about restoring essential business systems and technology infrastructure after a devastating incident.
Business continuity is about keeping a business operational during a disaster.
This is the backbone of your incident response readiness. It defines your incident response processes (which we’ll cover below) so there are no questions when the unthinkable occurs.
There is no one-size-fits-all approach to this plan. Here are some excellent resources on structuring your plan.
Some organizations may not have the bandwidth to create this plan on their own. An MSSP can help craft a plan that fits the unique processes and regulatory requirements governing your organization.
While your plan should include role assignments, it’s worth calling this out separately. Before an incident ever occurs, you want to have several roles filled, as CISA (the U.S. Cybersecurity & Infrastructure Security Agency) explains.
For midmarket organizations, it may be challenging to assign some or all of these roles in-house. For these organizations, an MSSP (managed security services provider) can assist.

The exact process you use will depend on your incident response plan. Different plans may use different terminology or combine certain steps together.
However, speaking generally, here are the steps involved in incident response and containment.
Incidents are typically detected by sophisticated software like MDR (managed detection and response), which may use powerful algorithms and even AI to spot anomalous behavior on your network. This allows your cybersecurity analysts to ignore harmless network traffic and focus on activity that looks suspicious.
Once automated systems have detected an incident, your cybersecurity specialists will identify it. This means gathering the specific information they need to contain the threat—such as systems affected, type of attack, IP address of origin, and more. Your specialists will begin a rigorous process of documentation that will aid not only in the incident response, but also in communication with law enforcement and in preparation for any potential legal action.
Once your cybersecurity analysts know what they’re dealing with, they’ll move fast to contain the threat.
Effective containment will mean different things depending on which systems are compromised. For example, if a workstation has malware installed on it, the first step in containment is to isolate that machine from the network and from all other machines. Cybersecurity specialists can do this remotely using software that still allows them to access the machine after it’s been cut off from the network.
If an essential device like a server is compromised, containment gets more complicated. Specialists must take into account the presence (or absence) of redundant server resources, as well as the potential impact to operations and revenue—both for leaving the server online, and for taking it offline. Experience and understanding of the scenario are essential for making the right decisions here.
Earlier in the process, your cybersecurity analysts had to prioritize containment over full analysis. This means they only gathered as much information as they needed to contain the threat.
Now that the threat is contained, it’s time to get the full story. Your cybersecurity specialists will uncover as much information about the incident as possible. They’ll consult SIEM (security information and event management) software, as well as any additional logs required. All along the way, they’ll continue to document everything they find to support communication with stakeholders, customers, and law enforcement—as well as providing an evidentiary foundation for responding to any legal action.
Now it’s time for your cybersecurity specialists to destroy the threat.
Eradication looks different depending on the type of attack, but here are some actions that typically occur.
You can’t go back to life as usual after eradicating a threat. The information gathered in the incident response process will offer numerous takeaways for making your environment more secure. The key is to turn that information into real changes to systems, hardware, and processes.
Here are some common changes that companies make during the recovery process.
Whatever changes have been implemented, it’s a good idea to test them for effectiveness. A network penetration test can determine how effective these changes are.
As you can see, it’s a fairly significant responsibility to develop and implement an incident response plan—then actually respond when an incident occurs.
Many midmarket companies don’t have the resources to achieve this in-house. IT staff have their hands full with day-to-day operations. This leaves no bandwidth for a programmatic approach to incident response, and it makes real-time containment and eradication almost impossible.
This is one reason MSSPs exist. The right partner can advise on the right incident response framework for your organization—and they can create a plan from that framework that’s tailored to your unique operations.
The key, though, is to insist on an MSSP who not only notifies you of incidents, but also remediates them.
Unfortunately, most MSSPs don’t actually remediate incidents. They only provide notification to their client (and/or to the client’s MSP or managed IT service provider). Under this model, incident response and containment gets broken up across multiple vendors and teams. This destroys any synergy across the process. It can lead to essential information getting lost and, at worst, incomplete attempts at containment and eradication.
Midmarket organizations without cybersecurity experts on staff should look for comprehensive MSSP coverage. Decent MSSPs will handle cybersecurity from top to bottom, including the entire incident response and containment process.
But the best MSSPs go beyond this. They offer cybersecurity service guarantees that cover the cost of their services to remediate an incident (with limitations).
That’s what we do here at Corsica Technologies. Our Corsica Service Guarantee empowers us to cover some or all of the cost of services to remediate incidents on our clients’ systems. As far as we know, this is the only service guarantee of its kind in the industry. See the link for details and limitations.
Want to learn more? Get in touch with us today. Let’s talk about your incident response and containment process—and how we can help.

💡 Compare Copilot vs. ChatGPT Get Your FREE Chart Originally published November 1, 2023. Completely refreshed March 31, 2026. Short answers: ChatGPT is better for

💡 Ready to improve your security? Talk to us about your challenges. Book a Consultation The recent cyberattack on Stryker, a leading manufacturer of medical

💡 EXCLUSIVE Resource: Cybersecurity ROI Calculator Try the Calculator In today’s cyberthreat environment, it can be tough to manage your firewall infrastructure on your own.
Corsica Technologies takes a flexible approach to incident response depending on the customer’s internal capabilities and their preferences. If a client has internal IT or cybersecurity staff, they may want Corsica to assume a collaborative role in incident response. If the client has no internal IT or cybersecurity staff, Corsica takes full ownership of incident response and containment.
In both scenarios, Corsica comes to the table with established best practices in incident response. The Corsica team works with the customer as needed to refine this approach and adapt it to the customer’s unique technology environment, cybersecurity risks, regulatory compliance needs, and operational preferences.
If an incident occurs, the Corsica team works through a well-defined playbook to respond, investigate the incident, contain it, eliminate the threat, and produce recommendations to prevent similar incidents in the future. At all stages of the response process, the Corsica team maintains continuous communication with the client, ensuring collaboration as needed.
MSSPs (managed security service providers) offer these services to shut down cyber attacks against their clients. Incident response and containment uses a variety of sophisticated tools, alongside experienced human vigilance, to lock down cyber attacks in real time and contain the damage.
Organizations of all sizes, in every industry, are vulnerable to cyber attacks. Criminals don’t discriminate between those who can afford a devastating breach and those who can’t. That means every company is in a better position with these services than without them.
Look for a partner who meets your needs in two essential ways:
Both components are critical. A partner can have all the right capabilities and services, but if they’re a real pain to work with, the relationship may cause more headaches than it’s worth.
On the other hand, a partner could be great to work with—but if they have inexperienced technicians or they don’t cover all your needs, then things still aren’t working.
In terms of capabilities and services, look for a partner who covers all your needs:
In terms of finding a provider who acts as a true partner, look for these characteristics:
Here at Corsica Technologies, we’ve got it all covered. From unlimited services to predictable pricing and a “can-do” company culture, we’re making life easier for the people we serve. Contact us today to see what life could look like as a Corsica client.
Most MSSPs claim to be a true partner, but they don’t deliver. Rather than valuing the relationship, they nickel-and-dime their clients when it comes to billing. Fluctuating ticket counts and workstations can create unpredictable invoices. This helps the service provider—but it doesn’t help you.
That’s why we’re fixing the cybersecurity support experience for companies that deserve better. We are the only managed service provider to offer unlimited technology services for one predictable price. That’s what makes us so different. It’s really that simple!
As far as our specific services, we cover essential initiatives like IT, cybersecurity, and digital transformation—but we also cover more technologies than most MSPs do. We also handle EDI and data integration services, which are highly specialized.
In other words, you can hand off as much of your technology to us as you want. And you can do it for one simple monthly price.
So no. We’re not just another MSP.
Want more details? See how Corsica compares to the alternatives.
Yes! We’re one of the few technology service providers who covers EDI solutions in addition to standard services like IT and cybersecurity support. Our career experts in EDI work closely with our cyber and IT teams to ensure all your essential systems run smoothly—with a strong security practice at the core.
In fact, this is one of your biggest advantages. It allows you to work with one provider instead of acting as a referee between different partners who don’t care about mutual success. Here’s how our coverage looks:
Absolutely! Our services are flexible. We can cover all your needs in a “fully managed” scenario—or we can act as an extension of your staff in a “co-managed” scenario. It all comes down to what resources you have today, what you need, and where your gaps and goals are.
Yes! Our services are designed to work around your needs. We are the team that will say YES to your requirements and what you need. We realize that when you need technology support you need a team that will respond and resolve quickly.
Contact us and let us know what you’re looking for.
Cybersecurity is a distinct need that requires constant monitoring as well as a strong strategy. If a threat arises, there’s no time to assemble a team to get up to speed. You need that team in place, and they need sophisticated tools to detect threats, respond, and defend your business. This is why companies turn to a cybersecurity service provider for help.
Absolutely! Our flagship service package, Corsica Secure, includes consulting from a vCIO/vCISO (virtual CIO/CISO). This C-level leader is a career expert in technology who works alongside you to plan out a 3-year technology roadmap, ensuring you never get blindsided by a technology investment.
We also offer project-driven consulting outside of our recurring services. Just get in touch with us to learn more!
Great question. Everything we do is ultimately about people, and you’ll see that reflected in our day-to-day interactions. You shouldn’t have to deal with techs who don’t care and can’t actually fix the problem. We only hire next-level humans who are career experts in their fields.
Our team is:
Our internal processes and operations are built for one purpose—to make life easier for you. To facilitate this, every client has expert personnel assigned to their journey:
As far as communication, our team is always available 24/7/365 for any technology problem. Because our pricing is simple, you’ll never get billed more when you need more. It’s all included. This empowers your team to go on doing what they do best—rather than fighting technology problems.
We’ll respond within 1 business day, or you can grab time on our calendar.