
The Stryker Cyberattack: Takeaways for Businesses
💡 Ready to improve your security? Talk to us about your challenges. Book a Consultation The recent cyberattack on Stryker, a leading manufacturer of medical
You get a single team handling cybersecurity, IT, and data integration services like EDI, filling the gaps in your team.
“Corsica is a one-stop shop for us. If I have a problem, I can go to my vCIO or a number of people, and you take care of it. That’s an investment in mutual success.”
– Greg Sopcak | Southern Michigan Bank & Trust
From 24/7 SOC services to MDR/SIEM, penetration testing and training, we’ve got you covered.
Get the expert support you need for your network, on-premises devices, VoiP, M365, Google Workplace, and everything in between.
Full support of compliance frameworks, including CJIS, HIPAA, CMMC, NIST, SOC 2, and more
Cut through the hype with smart strategies and right-fit AI solutions for your organization.
Take strategic steps with confidence as you collaborate with our expert business and vCIO consultants.
Get cloud security, integration, server virtualization, and optimization strategies to reduce your cloud costs.
Connect any data source to any other with robust solutions and managed services.
Stay ahead of the curve, eliminate waste, and grow revenue with next-generation technologies.
Expert consulting, implementation, integration, managed services, and cybersecurity for Microsoft products.
One program. One partner. Complete AI transformation.
It takes dedicated experience to use technology strategically in your industry. That’s why we specialize in certain verticals while offering comprehensive technology services.
From webinars and video tutorials to guides and blogs, we’ve got resources to help you and your team address any technology challenge.
Cyber criminals don’t wait for business hours to do their dirty work. Get the 24/7/365 monitoring you need to protect your customers, employees, networks, and data.



Advanced security monitoring is a set of active cybersecurity services that go beyond traditional, more passive measures such as antivirus software or firewalls. Advanced security monitoring typically includes:
It’s tough to keep up in today’s cyber threat landscape.
The average cost of a data breach is $4.88 million (IBM). Every organization has its vulnerabilities and specific risks, so foundational security alone is not enough. Your business needs advanced cybersecurity monitoring services to stay competitive, compliant, and secure.
Our in-house team of cybersecurity experts provides oversight and alerts at all levels, in addition to containment and remediation. We have the advanced knowledge and tools to monitor your network 24/7/365, stopping bad actors before they can access sensitive business data.

Get a better understanding of how your business activities affect your risks. We’ll ensure your devices and remote work setups are secure. Experienced industry veterans at Corsica Technologies analyze a year or more of data to find patterns, detect vulnerabilities, and create custom plans to enhance your security posture.
Rest easy knowing a team of highly credentialed professionals is watching over your infrastructure from our network operations center (NOC). Proactive approaches like this keep your organization ahead of potential threats. Experts at Corsica Technologies log activities day and night to protect your business from malware, botnets, data theft, and device breaches.
Remediate compromises immediately with assistance from our professionals, who routinely find and resolve incidents like zero-day threats. Our team uses sophisticated SIEM tools to identify breach attempts and analyze alerts. We’re also experts in post-incident forensics to gather evidence and assist in data recovery.
Pass audits and obey privacy regulations better with DataDefend. Our thorough oversight prevents incidents a lax compliance posture can create. Corsica Technologies IT professionals have expertise with regulations like GDPR that mandate active protection measures.
Stay responsive to shifting demands and business growth with a solution that adapts to your changing needs. The Corsica Technologies team automatically reallocates defense tools to meet your organization’s needs and goals, helping you achieve scalability.
Limit the chances of an incident and prevent downtime. Our proactive monitoring services help keep your infrastructure available and accessible. We’re so confident in what we do that we back it with the extensive Corsica Technologies service guarantee.

Unauthorized access to your systems via a server or computer
And other destructive programs that go unnoticed by even advanced antivirus
Covert, remote access and control of a computer to perform criminal activity
Covert, remote monitoring of device activity in order to gain intelligence
Spyware, keyloggers, and look-alike emails and websites that capture sensitive information
Software vulnerabilities unknown to the developer but known to hackers
Watch to learn more about what a SOC is and the role it plays in keeping businesses up and running. A Security Operations Center is the reporting point for a lot of different toolsets. A firewall or antivirus is no longer enough to protect your business. Advanced monitoring toolsets and techniques are required to detect and remediate cybersecurity threats.
Fill out this form, and we’ll respond within one business day. Let’s explore how we can support your business with robust cybersecurity services.
Welcome to the latest episode of Unraveling IT, Expert Tech Talks. I'm Nikita with Corsica Technologies, here to introduce our latest podcast featuring Ross Filipek, our our chief information security officer. In March 2024, Ross joined industry analysts at the IHL Group for an illuminating webinar on strategic technology and IT outsourcing for midmarket companies. Listen into this week's episode to hear our take on the top cybersecurity trends and threats for 2024. Enjoy. Hey, everybody. I'm Ross Filipek, chief information security officer at Corsica Technologies. I'll be talking about some cybersecurity trends and threats for 2024. And as a managed cybersecurity services provider, I think that Corsica is kind of in a unique position. We work with clients in a lot of different industries. So manufacturing, healthcare, finance, really all across the board. So I think we have, you know, some pretty unique perspective for observing some of these different cyber trends and threats, and I'm gonna be talking about, some big things that we're seeing out there. Just a high level agenda. Some of you probably will recognize a handful of these things as not necessarily being new for 2024, but rather these are the types of things that we continue to see organizations struggling with really, in all industries and all over the globe. So I think it's important to really hammer on those to talk about what we can do to mitigate risk from these types of things. And, you know, I hope it goes without saying, but this is gonna be a nonexhaustive list. Yeah. There's really no way I could capture every potential cyber threat and and trend for for 2024 in a single presentation. So I'm gonna focus on the types of things that we see the most of. So to start out, just to lay the groundwork a little bit, some background information. The cost of cyberattacks on the global economy is predicted to top ten point five trillion dollars by the end of this year. So if you try to wrap your mind around that figure, I mean, this is just, you know, it it it's mind boggling. I mean, clearly, cybersecurity is no longer something that we can just leave up to chance. So this really means that cybersecurity has to be treated as a strategic priority for us on an individual, organizational, and governmental level. Yeah. This is really why I'm such a proponent of conducting a proper cybersecurity risk assessment for your environment, you know, using a tried-and-true framework, you know, something like CIS RAM or the FAIR model. Yeah. Those are both great resources. But really, you know, if you guys think about the cybersecurity product marketplace today, there there are million products out there, you know, all kinds of security hardware and software and services. All those vendors position their products as kind of being the magic bullet for cybersecurity. But, unfortunately, there is no magic bullet when it comes to cyber, you know, and no organization has enough time or people or money to just go out and buy all the products to implement them. Right? You know, so we need some judicious way to figure out what do we really need from a safeguard perspective to protect our environments. You know, what's what's actually going to be effective for us to implement and what can we kind of put on the back burner. So that's really the purpose of conducting a cybersecurity risk assessment, so we know where to focus our protection efforts. Also, as Greg mentioned earlier, AI is gonna have a transformative impact this year on both attack and defense. Its impact is gonna be felt across every one of the trends that I'll cover here. I've got some more slides coming up about AI, so stay tuned. The cybersecurity skills crunch. As a managed cyber services provider, this one kinda hits close to home for me. But we've been seeing a shortage of professionals with the skills needed to protect organizations from cyber attacks continuing to be a running theme. And in fact, the research indicates that fifty four percent of cyber professionals believe that the impact of the skill shortage on their organizations has actually gotten worse over the past couple years. You could kinda see the graphic there, on the slide over on the right from the IHL study. Forty two percent of companies have IT staff availability as a top pain point. So this continues to be something that that we see. And, you know, for those of you who have ever tried to hire cybersecurity talent, you know, particularly good cybersecurity talent, those people tend to be expensive, they tend to be difficult to find, and they tend to be difficult to retain. So, you know, we really see that continuing to be a running theme. But efforts to rectify the situation include increasing salaries. So, you know, that's great, but you it can only only go so far before the economics just don't make sense. Certainly, greater investment in training and development and upskilling programs. You know, these are great ways to attract and retain skilled cybersecurity talent. But here again, you know, these things tend to be expensive and they tend to get more expensive over time. So as a result of this, we've really seen a dramatic increase in the amount of outsourcing to, manage providers with the necessary tools and skill sets. Generative AI for both good and evil. You know, we've talked about AI a couple times already, today. But as AI increases in sophistication, we're gonna continue to see more sophisticated and smarter AI powered attacks. These are gonna be things that range from deep fake social engineering to automated malware that in intelligently adapts to the detection. So, you know, kind of the classic example of this, if there is such a thing, you know, you guys remember, like, five years ago or ten years ago, it was usually pretty easy to spot phishing emails. You know, there'd be a lot of misspelled words and poor grammar. Really a lot of red flags that our users can be trained to be on the lookout for to spot a phishing email or, you know, some kind of social engineering attack, that's coming in and and reaching them. So really what we've been seeing as the result of generative AI tools are that cyber criminals, you know, particularly those who are not native English speakers, now have the ability to craft very believable, emails written in perfect English, no misspellings, no bad grammar. And now, you know, our our end users are having to contend with those types of attacks. So it it just really puts an additional burden on us as organizations because the number of red flags that are at our disposal to look for now is dramatically shrunk. So, you know, that's not to say that it's only the bad guys who are able to make use of AI. The good guys are having excellent results with it as well. So at the same time, AI is gonna help us detect and neutralize cyber threats thanks to things like real time anomaly detection, smart authentication, and some automated incident response capabilities. So, yeah, I could speak for Corsica as a managed cybersecurity provider. Many of the tools that we use to deliver our cybersecurity services and the tools that our security operation center uses to to monitor, those tools and and those services, already make heavy use of artificial intelligence. So they just really help our SOC analysts be much more efficient and effective and accurate when it comes to investigating and triaging cyber attacks. So I think, you know, definitely some some strong advantages for AI for the good guys as well. So, what we can say is that if cyber attacks and defense this year is like a game of chess, then AI is the queen. So whoever controls that has the ability to create powerful strategic advantages. Next level of phishing attacks. So, you know, this is certainly nothing new. Phishing has been a problem for a lot of organizations for a long time. It's going to continue to be a problem, you know, particularly, when used in conjunction with generative AI, like I was talking about on the previous slide. Saw a pretty interesting statistic, a couple of months ago, and that's that eighty percent of all successful cyber attacks actually target people, not computers. That makes sense. Right? You know, if you're an attacker, why do you wanna spend a month or a week, you know, a a week or a month or, you know, even a year trying to hack your way in to, you know, through somebody's firewall or hacking to somebody's server where you could just fish their employees and trick all those people into giving you their usernames and passwords. You know, attackers like to work smart, not hard. So certainly, they're gonna continue to hammer away at phishing until we get better at detecting and stopping it. So the response to this, yeah, kind of, like I implied a second ago is that it it'll largely revolve around organization wide awareness and education. So continuing to be aggressive about security awareness training for our employees, it's just gonna be so critical to do. You know, for for many clients, I recommend that if you're in a position right now where you're doing, like, a like, a big batch of annual cybersecurity awareness training, Look at splitting that up over the course of the year, so maybe move to a quarterly training model with a smaller volume of training courses. And the reason that tends to be more effective is that, you know, as long as we can routinely get this training information and testing, in front of our employees, that tends to keep these concepts fresh in memory and, you know, people, are are less likely to, you know, kinda put it on the shelf and and forget about it. IoT cyberattacks. So some of you probably recognize IoT. IoT is the acronym for Internet of Things. So when I talk about IoT devices, I'm talking about really any electronic gadget that connects to our network in some capacity, but it doesn't actually have a human user sitting behind it. So, you know, you think about nowadays, refrigerators and, you know, toasters and smart TVs are a great example. All these things, you know, people buy them and then they connect them to the network and then they tend to forget about them. So over time, a lot of these things wind up missing firmware updates and security patches. And really what that does is just, really, increases what we call the attack surface for our organizations. It gives those potential attackers a lot more that they could potentially grab on to and hammer away at to try to breach our environments. In addition, with the work from home revolution continuing, the risks posed by workers connecting or sharing data over improperly secured devices is gonna continue to be a threat. So, you know, I would imagine most of you, you know, certainly back during the pandemic, had a lot of employees working from home, you know, probably using personal devices, connecting to your, business environments across infrastructure that your IT department didn't necessarily have visibility into or the, control over. So that caused a lot of problems for a lot of organizations. Cyber resilience. So, I think two terms that a lot of times get used interchangeably but really mean two different things are cybersecurity and cyber resilience. But the distinction, I think, is becoming increasingly important. So while the focus of cybersecurity is on attack prevention and detection, the focus on cyber resilience is on response. So some of you may have heard the adage that it's not a question of if you get breached, it's a question of when you get breached. So from the cyber resilience standpoint, the more effort we can put into preparing for that inevitable breach, In other words, sitting down and taking the time to develop a proper incident response plan and then periodically testing that plan to make sure it's doing what we need it to do. Yeah. All the preparation we can do ahead of time is just gonna make life so much easier for us if we ever end up needing to respond to a breach. So very important to do. It's gonna be crucial going forward. Less than zero trust. Some of you may be familiar with what it's called the excuse me. Some of you may be familiar with what's called the zero trust framework. This is a model of network architecture that stresses that there's really no perimeter within which the network activity, can be assumed to be safe. So really what that means is, you know, you think about ten years ago, a lot of organizations were set up so that if employees were physically working in the office, you know, you had people coming in and working in their their offices or out of their cubicle. A lot of times, we set those up so those people could bypass things like multifactor authentication and many of the other cybersecurity controls that they would otherwise have to go through if they were trying to connect from the outside. Right? So what zero trust says that we do is kinda flip that model on its head And it says that we should assume that all of the devices in our environment, whether they're devices in our offices or the devices that our users are using to connect from home or from hotel rooms. We should assume that all those things are compromised. So we're gonna take other measures to protect our organization's data. And, generally, that amounts to very granular, very accurate authentication and authorization mechanisms for that data. But, for those of you who are familiar with CISA, that's the US government's, cybersecurity and infrastructure security agency. They recently put together a really great white white paper on zero trust architecture that does a fantastic job of explaining what that is conceptually. So, you know, if that if that's the type of thing that interests you, I'd really encourage you to, check out that that CISA white paper. It's a great reference. Cyber warfare and state sponsored attacks. Yeah. These have been going on for a long time. They're not gonna let up anytime soon. And, you know, I think for for the rest of, yeah, the rest of our existence, we're we're gonna have to continue to deal with these things. So, certainly, the war in Ukraine, has exposed the extent to which nation states are willing and able to deploy cyber attacks. Against both military and civilian infrastructure. And, you know, that that we're we're not just seeing that in Ukraine, you know, certainly with Israel and Gaza. This is a big deal as well. Going forward, wherever military operations take place around the world, they're gonna go hand in hand with cyber warfare operations. If physical warfare and cyber warfare are gonna be inseparable, they're always gonna go together. So the most common attacks that we continue to see originated from state sponsored actors are phishing attacks. You know, like I mentioned a few minutes ago, eighty percent of all successful breaches start with phishing. Attackers know this. They know it's highly effective. So that continues to be what they focus on. So being able to gain access into their victim environments to do disruption and espionage And even things like denial of service to knock systems offline, you know, that that tends to be the hallmark of these state sponsored threat actors. Separately from warfare though, we've got major elections coming up this year in the US, in the UK, in India, and we can expect to see an increase in cyberattacks that are aimed disrupting those processes. And lastly, we are continuing to see a trend toward soft skills becoming increasingly essential for cybersecurity professionals. So, you know, I can tell you, you know, ten years ago, fifteen years ago, when we would hire a talented, you know, cybersecurity engineer, chances are pretty strong that we'd end up putting him or her in, know, in a closet someplace and just having them focus on malware analysis or, you know, doing the technical things to detect cyber threats in the environment. And that worked well for that time. But, you know, if you think about today, cybersecurity is just so tightly woven into all of our business processes and all of the information technology that we use across our organizations. It's just becoming so important for those who are tasked with cybersecurity for our environments to be able to communicate effectively with all the rest of our employees. So, yeah, certainly the soft skills, we we definitely put a premium on. And I think, unfortunately, a lot of times, you know, that just, you know, continues to make it more difficult to find, people who are able to do what really needs to be done. But, yeah, certainly, this is gonna be a trend that continues and is just gonna get more important as the years go on.

💡 Ready to improve your security? Talk to us about your challenges. Book a Consultation The recent cyberattack on Stryker, a leading manufacturer of medical

💡 EXCLUSIVE Resource: Cybersecurity ROI Calculator Try the Calculator In today’s cyberthreat environment, it can be tough to manage your firewall infrastructure on your own.
💡 EXCLUSIVE Resource: GenAI Policy Template Download Now AI is now embedded in the vast majority of enterprises. That’s not a projection. That’s today’s reality. But universal AI adoption hasn’t been matched
Large enterprises typically have the resources they need to hire cybersecurity experts in-house.
For the rest of us, it’s tough to keep up with cybersecurity. A good MSSP (managed security services provider) is flexible, ready to provide fully managed services (if you don’t have a team) or co-managed services alongside existing staff. It’s all about covering your gaps.
In fact, a comprehensive MSSP steps in exactly where they’re needed. If the company also handles other disciplines, as Corsica does, they can provide diverse services such as:
If you need help with any of the above, a service provider like Corsica is the answer. That’s why we’re here!
Look for a partner who meets your needs in two essential ways:
Both components are critical. A partner can have all the right capabilities and services, but if they’re a real pain to work with, the relationship may cause more headaches than it’s worth.
On the other hand, a partner could be great to work with—but if they have inexperienced technicians or they don’t cover all your needs, then things still aren’t working.
In terms of capabilities and services, look for a partner who covers all your needs:
In terms of finding a provider who acts as a true partner, look for these characteristics:
Here at Corsica Technologies, we’ve got it all covered. From unlimited services to predictable pricing and a “can-do” company culture, we’re making life easier for the people we serve. Contact us today to see what life could look like as a Corsica client.
Most MSSPs claim to be a true partner, but they don’t deliver. Rather than valuing the relationship, they nickel-and-dime their clients when it comes to billing. Fluctuating ticket counts and workstations can create unpredictable invoices. This helps the service provider—but it doesn’t help you.
That’s why we’re fixing the cybersecurity support experience for companies that deserve better. We are the only managed service provider to offer unlimited technology services for one predictable price. That’s what makes us so different. It’s really that simple!
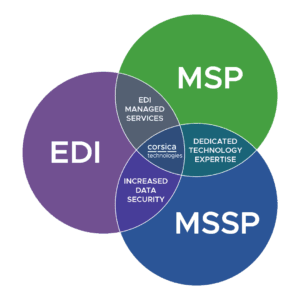
As far as our specific services, we cover essential initiatives like IT, cybersecurity, and digital transformation—but we also cover more technologies than most MSPs do. We also handle EDI and data integration services, which are highly specialized.
In other words, you can hand off as much of your technology to us as you want. And you can do it for one simple monthly price.
So no. We’re not just another MSP.
Want more details? See how Corsica compares to the alternatives.
Yes! We’re one of the few technology service providers who covers EDI solutions in addition to standard services like IT and cybersecurity support. Our career experts in EDI work closely with our cyber and IT teams to ensure all your essential systems run smoothly—with a strong security practice at the core.
In fact, this is one of your biggest advantages. It allows you to work with one provider instead of acting as a referee between different partners who don’t care about mutual success. Here’s how our coverage looks:
Absolutely! Our services are flexible. We can cover all your needs in a “fully managed” scenario—or we can act as an extension of your staff in a “co-managed” scenario. It all comes down to what resources you have today, what you need, and where your gaps and goals are.
Yes! Our services are designed to work around your needs. We are the team that will say YES to your requirements and what you need. We realize that when you need technology support you need a team that will respond and resolve quickly.
Contact us and let us know what you’re looking for.
Cybersecurity is a distinct need that requires constant monitoring as well as a strong strategy. If a threat arises, there’s no time to assemble a team to get up to speed. You need that team in place, and they need sophisticated tools to detect threats, respond, and defend your business. This is why companies turn to a cybersecurity service provider for help.
Absolutely! Our flagship service package, Corsica Secure, includes consulting from a vCIO/vCISO (virtual CIO/CISO). This C-level leader is a career expert in technology who works alongside you to plan out a 3-year technology roadmap, ensuring you never get blindsided by a technology investment.
We also offer project-driven consulting outside of our recurring services. Just get in touch with us to learn more!
Great question. Everything we do is ultimately about people, and you’ll see that reflected in our day-to-day interactions. You shouldn’t have to deal with techs who don’t care and can’t actually fix the problem. We only hire next-level humans who are career experts in their fields.
Our team is:
Our internal processes and operations are built for one purpose—to make life easier for you. To facilitate this, every client has expert personnel assigned to their journey:
As far as communication, our team is always available 24/7/365 for any technology problem. Because our pricing is simple, you’ll never get billed more when you need more. It’s all included. This empowers your team to go on doing what they do best—rather than fighting technology problems.
We’ll respond within 1 business day, or you can grab time on our calendar.