
9 Common Signs of a Phishing Attack
Phishing is a social engineering tactic cybercriminals use to lure sensitive data via emails. Take our Quiz & see if you recognize phishing red flags.
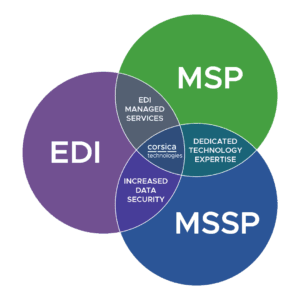
You get a single team handling cybersecurity, IT, and data integration services like EDI, filling the gaps in your team.
“Corsica is a one-stop shop for us. If I have a problem, I can go to my vCIO or a number of people, and you take care of it. That’s an investment in mutual success.”
– Greg Sopcak | Southern Michigan Bank & Trust
From 24/7 SOC services to MDR/SIEM, penetration testing and training, we’ve got you covered.
Get the expert support you need for your network, on-premises devices, VoiP, M365, Google Workplace, and everything in between.
Full support of compliance frameworks, including CJIS, HIPAA, CMMC, NIST, SOC 2, and more
Cut through the hype with smart strategies and right-fit AI solutions for your organization.
Take strategic steps with confidence as you collaborate with our expert business and vCIO consultants.
Get cloud security, integration, server virtualization, and optimization strategies to reduce your cloud costs.
Connect any data source to any other with robust solutions and managed services.
Stay ahead of the curve, eliminate waste, and grow revenue with next-generation technologies.
Expert consulting, implementation, integration, managed services, and cybersecurity for Microsoft products.
One program. One partner. Complete AI transformation.
It takes dedicated experience to use technology strategically in your industry. That’s why we specialize in certain verticals while offering comprehensive technology services.
From webinars and video tutorials to guides and blogs, we’ve got resources to help you and your team address any technology challenge.
Employees are your front line of defense in today’s cyber threat landscape. Give them the comprehensive, accessible training they need to keep your organization secure.


It’s tough to keep up as criminals reinvent their tactics.
Unfortunately, phishing emails, texts, and bad actors using AI tools represent a significant threat for organizations that are unprepared—particularly those that don’t have a cyber security managed services provider. Human beings are the weakest link in any security program, and that’s especially true when it comes to phishing emails.
Make sure your team is informed, tested, and up-to-date on the latest threats like spear phishing, whaling, smishing, cross-site scripting attacks, and more.


Our team of experts has 250+ combined years of experience keeping businesses safe in this evolving threat landscape. We’ll assess your business for security risks and help you build a proactive plan that keeps you, your employees, and your data secure.
The best part? We offer the only Cybersecurity Service Guarantee in the industry. We cover the cost of our services to remediate an incident, with limitations.
You guys have done a great job educating my people because, you know, we were getting so many emails and all this stuff and everybody was afraid. Right? Mhmm. You don't know if it's real, and all this other stuff, but we didn't know how to educate them. That's where you guys came in and you guys did a very good job of educating my people. So we went from being afraid to being aware. Mhmm. And that's, that's a huge shift. Welcome back to Unraveling IT: Expert Tech Talks. My name is Nate Troyer. I'm an account executive at Corsica Technologies. I'm interviewing Rick Melvin from Powell Tool. He's the president of the company. Today, we're gonna be talking about their strategy with IT and how they came to be partners with Corsica. Rick, nice to have you. Thank you. Glad to be here. Can you give us some background on, on Powell Tool, how it's integrated technology, and, and what your role is at the company? Sure. So Powell Tool, we're a, precision cutting tool distributor servicing the manufacturing market, many industries. We have been in business since 1948. So we're currently celebrating our- That's a long time. 77th year. Yes. Thank you. Mhmm. We're excited. We're proud of that. We're on our third generation of ownership. We're a family owned company. We have 22 amazing employees. We all work together as a unit, and we give our customers and our vendors the best service that we can give. We've been computerized since the late 1950s, early 1960s, somewhere in that neighborhood. I wasn't there, actually. Were those computers big? Well, they were huge. The room we have is still humidity controlled, air controlled, and there's one server rack in it where it's bigger. It's twice the size of this room. So it used to be that big, and now they're just a server rack? Just a server rack. Wow. Yep. Wow. So it's pretty interesting. And, and now we'll get into this a little more, but we've, you know, but now we've decided to eliminate on, on-prem servers, and we've gone to cloud based pretty much for our entire business with Corsica. So that's an interesting segue. When did you guys make that decision, and why? It didn't happen overnight, Nate. It wasn't like a light switch on or off. It kind of happened over time. And, and how it happened was we started with Teams, Microsoft Teams. That's how it started. And the reason that we started that was because we have nine outside salespeople in a pretty vast territory, and we were bringing everybody together once a quarter, for quarterly meetings. Mhmm. And I just found that to be very ineffective use of time. And one of our primary vendors, SECO, they were just getting into using Microsoft Teams, and they kind of turned me on to it. Okay. And it helped me get it going. And so we started with that using it with my outside sales team specifically to have quarterly meetings where they could do it remote and not have to travel all the way to the office. And it worked very well because we did that two years before COVID. So, Al, so you guys were re you guys were kinda ready? We were kind of already ready to run. And right before COVID, we switched all the outside guys to Microsoft Office 365. Mhmm. So we moved all of our email to that for them. You know, they had all the suite of Microsoft offerings, along with their Surface tablets that they use, you know, to do their job and stuff like that. So we had kind of a half and half system in that point because the outside guys, my team, was on the cloud Mhmm. And all of our inside were still on on-prem servers. So we kinda have that divided where my wife runs the inside and I kinda run the outside. That's kind of how we handle management of the company. So with that being said, then after COVID, then we were making the decision to switch over the rest of the company to Office 365. So we did that. And then after we did that, we switched our ERP, and we went with NetSuite, which is an Oracle product Mhmm. Which is we're very happy with it, by the way. I really like it. And that is in the cloud. So now we had our email, our files, and our ERP in the cloud. And then our BI tool had been I forgot about that. That's been in the cloud for a long time. We have Focus, and we've been using them for- So it seems like it was just, like, step by step, by step, by step. And I think and that that was the more logical way for us because, you know, being a, a, a medium sized company, you know, there's you wear a lot of hats, everybody in the organization. So to be able to flip a switch like that, like, we don't have an IT department. We don't have things like that. So you have to do them in in increments. I, I kinda wanna jump off that a little bit. How did you guys handle IT prior to your partnership? Since you I think you have a tech technical background. Right? I do. Yes. So years ago, I did programming, and I did, did some things for my other company just because I was by default, I was the most knowledgeable. So, I would be the one to learn it and execute it. But yeah. So, what we did was we had another IT company that we were using, and it had gotten to the point where the person that was dealing with them was getting very frustrated, and she was getting ready to retire. And so what we did was we were planning to do a review, you know Mhmm. Of our whole IT and decide what we wanted to do and where we wanted to go. Had you used managed services for, like, a long time, or, or had it been, like, primarily your responsibility and then suddenly there was a shift to managed services. It my responsibility when I came into I, I came into the company eight years ago. Okay. So prior to that, I was at my other company for 34 years doing Yeah. Sales related stuff. So we had we had always outsourced Well, we had an IT department at one point. Mhmm. But then at when we had lost IT people or they moved on, it became harder and harder to find IT people, and that's when we went with a, a service company. And I think they were just coming out at that time to realizing that, you know, hey. Let's try to make it easier for people to Yeah. So that's Utilize. So you were kinda like on the you've been on the bleeding edge of that sort of service because I think we've talked about this on another podcast. I think there's an awakening right now happening with within organizations, you know, specifically manufacturing, who are just looking at the landscape and saying, why do I have why have I hired a system engineer? Why have I hired a security engineer when Right. What they want to do is in their title? Right? They wanna engineer things. So after something's engineered, what are they doing all day? Right. And I think I think we're seeing a lot of people in those roles start to move and work at an MSB because then they get to do what they, they wanna do all the time. And it's so interesting that you say that. You kinda saw that you were reading those tea leaves really early on. Well, it That was hard to find people, one. Right? It was. But it was it was also too out of necessity because, like you said, once they get things done and once they get it set, now they're basically maintenance people. Right. Or less. You know, they're troubleshooting. They don't even wanna be that. They're doing exactly. So it's a whole different mindset. So we, we did sit down and we said, you know, what do we wanna do? Do we wanna hire IT, and what do we need? And one of the big things that came about was cybersecurity. Yep. And we're a member of AD, Affiliated Distributors, which you guys are Yep. A service provider for, and, actually, that's how I got your name. It's a great organization. So that's a shout out to AD doing their job, you know, making me aware of you guys. So that that's how the ball started rolling with you guys. But prior to us talking, we did sit down, you know, our management, me and my wife, and decided, you know, what path we wanted to take. So we decided that if we hire someone, well, now they gotta be up on cybersecurity, and they gotta be up on database. They gotta be up on what's going on in the cloud and all this other stuff. And it's just it's so much Mhmm. That, you know, I don't think one person can do it all. I don't think one person wants to do it all. Yeah. I mean, I just don't think it's possible, to be honest. Not effectively anyway. Right. And then, like you said, once you get to the point where all that stuff is set up, although I don't think cybersecurity is ever gonna go away now with what's happening in the world, but I, I think that's something. And, you know, it it's one of those things where at AD, we had we had the person talking to us about cybersecurity, and you guys have done a great job educating my people because, you know, we were getting so many emails and all this stuff, and everybody was afraid. Right? Mhmm. You're afraid to click on anything. You hurt. You don't know if it's real and all this other stuff. So we had to get them educated, but we didn't know how to educate them. That's where you guys came in, and you guys did a very good job of educating my people. So we went from being afraid to being aware. Mhmm. And that's, that's a huge shift because when when people are afraid to do something in their job, it it's not a good feeling. I don't care what position you hold in the company. It's not it's just not good. You can do, like, a decision paralysis where now you're not doing anything because you don't know what to do. Or, or you do something too quick Yep. Or without thinking or whatever. And that's the biggest thing that I took away from the security training was slow down. Mhmm. Just slow down. You know? And I tell my people all the time, you can't unring a bell. Right. Make sure you wanna ring that bell. That's all. Slow down. Mhmm. So that, that was really good. So we were we were very happy with that. One other thing I wanted to tell you about, you know, our, our journey to partnering with Corsica was one of the things that we really wanted was I wanted a company that understood, like, I needed you to be my IT. Mhmm. Meaning, if I need help with cybersecurity, I go to you. If I need help with servers, I go to you. If I need switch it, whatever. And you guys then bring to me, which Nathan has already started doing Mhmm. Start bringing to me Not me, Nathan. Somebody else. Nathan Minor. Start bringing things to me that say, hey, this is what you have and this is what we suggest you should go to and here's why. So it it's very much not just like, oh, you need a new switch. It's why. Strategic guidance. And, and here's why, and here's what it's gonna give to you as opposed to just boom, which is, you know, what we had before where it was very reactionary, and you guys are more proactive. And that's what I want. I don't want to only call you when I have a problem because that's just why did that problem occur? Why did it exist? And, and really anybody can do that. That's that doesn't differentiate us from anybody else. Correct. So, I appreciate that. Looking ahead, what are some of the key initiatives for Powell Tool Supply in the future given, given the landscape? I mean, you you've already talked about some of the ways you've, read the tea leaves. So what are you reading right now as far as from a business standpoint? What are the, what are the long reaching goals and objectives for business? The, the biggest goal that we have is to make Powell Tool easy for our customers and our vendors to do business with. Which is actually the same goals as our as, as our primary goal tool. Well, see that is that's in alignment. Yep. So and, and because that's the key to it. Right? I mean, we, we are the type of person. We provide very good service. My, my outside salespeople, they're highly trained. They're highly skilled. They can walk into a machine shop, and they can just hear a CNC machine, and they can tell that that's not running right. It's amazing. That's great. The training that they have. And so the point is we're just not selling things. We're selling solutions, and we're selling service. That that's what we do. So we go in and we help customers get the best solution for what they're trying to accomplish. Did you just read our mission and vision statement and just replaced your name? Because that's so close to what we do. We say, like, we're providing the outcome that you want. Right? We're providing solutions. That's all we talk about. I mean, that's probably why we're so well aligned. And it sounds like you guys are trying to do that as well in your own market vertical, which is pretty cool. Right. So what are some of the key takeaways that that you've had from just exploring more of the cybersecurity landscape? You said that we've helped you guys on your, your end users with their knowledge of just cybersecurity, and ninety six percent of breaches happen through end users. They click on something. Yep. What are what are some of the key takeaways that you've had from just having a little bit more immersion and consulting within the cybersecurity space? I've seen a shift in the reduction of anxiety from my employees. Really? Because, you know, you hear about we, we have a primary vendor of ours that got hacked really bad Mhmm. And, you know, makes everybody afraid. And now you get emails from what look like real vendors or customers, and you have to be really diligent to, to ferret it out. Is, is it real or is it not real? Right? So, a lot of times, they would funnel all that through me. And now we've got it to where they can make the same decision I'm going to make with the training that they've received because now they're more confident, not to the point of doing it wrong. Right. They're, they're confident in what they should do. Yep. You know, and when they should say, I'm not sure. That's the other thing. It, it was very apparent when after we did this cybersecurity training and we had a all-company meeting, we have one once a month, and the comments that everybody was flashing back and forth about the things they didn't know, they didn't realize how much of a problem it was out there in the world. You know, because we see it from our narrow viewpoint. Yep. Right? Yep. We only see what we see. We you don't know what you don't know. I say that all the time. So that's one of the things is that they, they felt that we're all back on the same track and that team. Do they because it kinda Do they think they're more equipped now? Like, they, they have they have they have some they have some way to differentiate falsehood from truth when it comes to the cybersecurity space? I, I think so. I think they're, they're confident without being cocky. Yeah. And they're aware without being afraid. Do you feel do you feel more confident in your, your business being able to, you know, have some sort of continuity if an event were to happen now that you now that you're working with Corsica? I think so. I mean, I think that the things that you guys are doing, we've only had a couple instances Mhmm. Where we had to get involved. And, you know, Corsica brought it to my attention immediately, and, you know, you guys shut it down Yep. Stopped it. Yep. I found out what was happening and who was doing it, and I went and this was early on. So this was even before the security training. Yep. So, you know, come, come to find out someone was doing something that they shouldn't have been doing, and they didn't really understand why. So we had to educate them, stop them, and then educate them. I I mean, I think I think the, the, the statement that that we say in our industry all the time is incidents happen all the time. It's, it's not letting them become events. Right? That's where we, that's where we step in. So then and that's actually a technical term in cybersecurity. We've had an incident, incident, incident, but the idea is to have so much visibility that you can go, boom, you stop the incident immediately. There's no fallout. It doesn't become a event. So But I do, I do feel confident that with those couple things that happened, it showed what we have in place now that we did not have before. So, yes, I am more confident. And and what I'm trying to do is I'm trying to, like, let you guys take care of this so that I can go back to running my business. Right. You know, because that's what I have to do. Yeah. Do you have some sort of peace of mind now? I do. I mean, it's, it's better. It, it I don't think I'll ever have a hundred percent with this Oh, no. There's no silver bullet of anything. But, yes, it's, it's much better. I'm, I'm much more confident that if something were to happen, we would be able to isolate it, eliminate it, and continue to operate as a business. So we've taken those steps so that I have a disaster recovery plan in place with you guys. So Great. Rick, I really appreciate you being here. I appreciate you allowing me to interview you as best I could. And I, I really appreciate your partnership with us. No. Thank you. And we're, we're excited, and, you know, you guys have what I really like is I'm a big person of do what you say. And you guys have done what you said you were going to do from day one, the first time I talked to you. So I'm, I'm very happy about that. That means a lot to me, and I know that a lot of people like me. That is extremely critical because you need to be able to rely on your partners. A true partner cares about my business as much as you care about your business and vice versa. Mhmm. I care about your business as much as I care about my business because we both wanna succeed. Mhmm. That's how we perceive our customers. That's how we perceive our vendors, and that's how we perceive our partners. So that's something that's extremely important to us as an organization and as people. So that I wanted to tell you guys thank you for that. Well, appreciate it. Hey. That was well said. Yeah. Thanks.
Get the comprehensive cybersecurity team you need for roughly the cost of ONE staff hire. Our team handles monitoring, threat detection, remediation, and more, while you focus on your core business.
Get the security operations center you need with a team that works 24/7/365. Our SOC never sleeps as we protect your data, systems, customers, and internal users from emerging cyber threats.
Are you backing things up as you should? Get peace of mind knowing your data is secure. Our solutions cover two essential components—data backup PLUS disaster recovery plans and processes.
If you can’t detect a cyberattack, you can’t even respond. Managed detection and response gives you the technology, the people, and the monitoring processes to lock down cyberattacks.
Who’s checking your patches? Do they have the time and energy for this essential function? Let our team manage your patching (Windows and third party) so you can focus on your core business.
Are you easy to hack? How would you even know before the unthinkable happens? Penetration testing puts your systems through a rigorous evaluation. You get actionable steps to improve security.
Regulatory compliance is challenging in today’s complex technology environment. Get the managed services you need to achieve continuous IT compliance with your framework or standard.
It’s impossible to eliminate risk. But what if you could quantify it—PLUS define a threshold of acceptable risk and take action to improve? It all starts with a cybersecurity risk assessment from our team.
Cybersecurity awareness training is an educational process that empowers users to detect and respond to common cyber threats. This type of training usually covers topics such as social engineering, pretexting, and phishing–including specific types of phishing such as whaling, spear phishing, smishing, and executive impersonation.
Companies choose to engage in cybersecurity awareness training for a variety of reasons.


Phishing is a social engineering tactic cybercriminals use to lure sensitive data via emails. Take our Quiz & see if you recognize phishing red flags.

Download phishing examples Can your employees spot a phishing email? One of the best ways to avoid getting tricked is to know the red flags

💡 EXCLUSIVE Guide: Phishing Email Examples Download Now Last updated April 1, 2026. If you’ve ever received an “urgent” email that didn’t quite seem legitimate,

The easiest way for cyberattackers to infiltrate an organization is through your employees. And phishing emails continue to get more convincing, especially with the help

Phishing is a social engineering tactic used by hackers to gain access to a network through an unsuspecting email click or attachment download. Since 91% of

Knowing how to spot phishing attacks is the best defense against falling victim to them. Keep your business network safe using these tips.
Watch to learn more about what a SOC is and the role it plays in keeping businesses up and running. A Security Operations Center is the reporting point for a lot of different toolsets. A firewall or antivirus is no longer enough to protect your business. Advanced monitoring toolsets and techniques are required to detect and remediate cybersecurity threats.
Fill out this form, and we’ll respond within one business day. Let’s explore how we can support your business with robust cybersecurity services.
Large enterprises typically have the resources they need to hire cybersecurity experts in-house.
For the rest of us, it’s tough to keep up with cybersecurity. A good MSSP (managed security services provider) is flexible, ready to provide fully managed services (if you don’t have a team) or co-managed services alongside existing staff. It’s all about covering your gaps.
In fact, a comprehensive MSSP steps in exactly where they’re needed. If the company also handles other disciplines, as Corsica does, they can provide diverse services such as:
If you need help with any of the above, a service provider like Corsica is the answer. That’s why we’re here!
Look for a partner who meets your needs in two essential ways:
Both components are critical. A partner can have all the right capabilities and services, but if they’re a real pain to work with, the relationship may cause more headaches than it’s worth.
On the other hand, a partner could be great to work with—but if they have inexperienced technicians or they don’t cover all your needs, then things still aren’t working.
In terms of capabilities and services, look for a partner who covers all your needs:
In terms of finding a provider who acts as a true partner, look for these characteristics:
Here at Corsica Technologies, we’ve got it all covered. From unlimited services to predictable pricing and a “can-do” company culture, we’re making life easier for the people we serve. Contact us today to see what life could look like as a Corsica client.
Most MSSPs claim to be a true partner, but they don’t deliver. Rather than valuing the relationship, they nickel-and-dime their clients when it comes to billing. Fluctuating ticket counts and workstations can create unpredictable invoices. This helps the service provider—but it doesn’t help you.
That’s why we’re fixing the cybersecurity support experience for companies that deserve better. We are the only managed service provider to offer unlimited technology services for one predictable price. That’s what makes us so different. It’s really that simple!
As far as our specific services, we cover essential initiatives like IT, cybersecurity, and digital transformation—but we also cover more technologies than most MSPs do. We also handle EDI and data integration services, which are highly specialized.
In other words, you can hand off as much of your technology to us as you want. And you can do it for one simple monthly price.
So no. We’re not just another MSP.
Want more details? See how Corsica compares to the alternatives.
Yes! We’re one of the few technology service providers who covers EDI solutions in addition to standard services like IT and cybersecurity support. Our career experts in EDI work closely with our cyber and IT teams to ensure all your essential systems run smoothly—with a strong security practice at the core.
In fact, this is one of your biggest advantages. It allows you to work with one provider instead of acting as a referee between different partners who don’t care about mutual success. Here’s how our coverage looks:
Absolutely! Our services are flexible. We can cover all your needs in a “fully managed” scenario—or we can act as an extension of your staff in a “co-managed” scenario. It all comes down to what resources you have today, what you need, and where your gaps and goals are.
Yes! Our services are designed to work around your needs. We are the team that will say YES to your requirements and what you need. We realize that when you need technology support you need a team that will respond and resolve quickly.
Contact us and let us know what you’re looking for.
Cybersecurity is a distinct need that requires constant monitoring as well as a strong strategy. If a threat arises, there’s no time to assemble a team to get up to speed. You need that team in place, and they need sophisticated tools to detect threats, respond, and defend your business. This is why companies turn to a cybersecurity service provider for help.
Absolutely! Our flagship service package, Corsica Secure, includes consulting from a vCIO/vCISO (virtual CIO/CISO). This C-level leader is a career expert in technology who works alongside you to plan out a 3-year technology roadmap, ensuring you never get blindsided by a technology investment.
We also offer project-driven consulting outside of our recurring services. Just get in touch with us to learn more!
Great question. Everything we do is ultimately about people, and you’ll see that reflected in our day-to-day interactions. You shouldn’t have to deal with techs who don’t care and can’t actually fix the problem. We only hire next-level humans who are career experts in their fields.
Our team is:
Our internal processes and operations are built for one purpose—to make life easier for you. To facilitate this, every client has expert personnel assigned to their journey:
As far as communication, our team is always available 24/7/365 for any technology problem. Because our pricing is simple, you’ll never get billed more when you need more. It’s all included. This empowers your team to go on doing what they do best—rather than fighting technology problems.
We’ll respond within 1 business day, or you can grab time on our calendar.