COVID-19 caused a mass shift to telework for many industries, and healthcare was no exception. Because patient care is a priority–especially during a pandemic–many healthcare organizations scrambled to accommodate work-from-home setups without ensuring that proper cybersecurity measures were in place. While this had a positive effect on the continuity of care, it left these organizations increasingly vulnerable to cyber-attacks.
What Is Protected Health Information (PHI)?
The Health Insurance Portability and Accountability Act or (HIPAA) is a law that went into effect in 1996 to protect an individual’s health information from falling into the wrong hands. Under HIPAA, healthcare plans and providers must protect patients’ health information in storage, use, and transit so that only authorized individuals are able to access it. Organizations that fail to do this are subject to significant penalties.
Protected Health Information (PHI) is defined as any health information related to past, present, or future physical or mental health conditions of an individual. This also includes the past, present, or future payment for the provision of healthcare for that individual. HIPAA protects PHI in different locations such as:
- Transmitted by electronic media,
- Maintained in electronic media; or
- Transmitted or maintained in any other form or medium.
PHI includes all Individually Identifiable health information that can be used to identify contact or locate a person. There are currently 18 identifiers that must remain protected, which include patient phone numbers, email addresses, Social Security Numbers, health insurance beneficiary numbers, and any recognizable photographic images.
PHI does not, however, include or protect the individually identifiable health information of an individual who have been deceased for more than 50 years
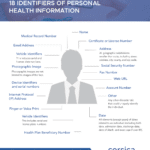
Download Our PHI Identifiers Infographic
Why Do Cybercriminals Want PHI?
As of 2019, the healthcare industry had the 4th largest number of data breaches among the top five business sectors in the U.S. These sectors include, in order of the number of breaches from highest to lowest:
- Financial services
- Retail
- Government
- Healthcare
- Manufacturing
Insurance information or health information about a person is ten times more valuable on the black market than credit card information. You can get a new credit card number if yours is stolen, but you can’t get a new health history. This means that healthcare professionals must be vigilant to ensure that patient records are secure.
Cybercriminals can take PHI and commit multiple types of fraud or identity theft. With this medical information, cyber-criminals could also gain access to prescription medication, receive medical care, and obtain access to an individual’s financial information
According to Interpol, cyber-criminals have consistently sought to take advantage of organizations that rapidly deployed remote systems and networks to support the shift into a remote workforce. Hackers have also targeted the increase in security vulnerabilities to steal data, disrupt operations, and generate profits. These reports also showed a 59% increase in phishing, scams, and fraud. 47% of reported healthcare data breaches in the first six months of 2020 were initiated by email-based attacks, which have increased from 42% at this time last year.
So far in 2020, more than 5.6 million patient records have been breached this year alone
Who Is Responsible for Protecting PHI?
Any organization that interacts with PHI is responsible for protecting it, and this responsibility flows down to that organization’s employees. This means that if you treat patients, access or update patient information in an EMR system, provide technology support for PHI-relevant information systems, or interact with PHI in virtually any other way, you are responsible for doing so in a HIPAA-compliant manner. And liability for violations isn’t limited to the offending organization as a whole. In certain cases, HIPAA violations can result in criminal indictments of individual employees, and the penalties can be severe.
According to the HHS, “Individuals, organizations, and agencies that meet the definition of a covered entity under HIPAA must comply with the Rules’ requirements to protect the privacy and security of health information and must provide individuals with certain rights with respect to their health information.”
Employee training is crucial to the success of your organization’s ability to comply with HIPAA. Having a dynamic training program that teaches your employees about the latest criminal techniques is imperative. Interactive click-based user training that focuses on PHI protection is just one of the training techniques we use.
View Our HIPAA Resource Center Here
What Are Some Best Practices for Protecting PHI with a Remote Workforce?
Remove smart devices (e.g., smart TVs, Amazon Alexa, and Google Assistant) from your remote location – smart devices are built to eavesdrop and record conversations.
- Keep communications digital and encrypted – Microsoft 365 optionally offers data Loss Protection (DLP) which screens outgoing emails for PHI and automatically encrypts emails that contain sensitive
- Set computers to lock after inactivity – working remotely has its distractions so enabling screen lock after a short period of inactivity will reduce the risk of drive-by viewings.
- Limit access to your systems – adopt a least privilege approach to your systems and make sure users only have access to the files and systems they need.
- Enable Multi Factor Authentication– MFA will help minimize the risk of non-employees accessing an information system using the device that may contain PHI.
- Disable the use of removable media storage– devices that have access to PHI should not allow USB drives or portable media drives to copy or move any PHI data from the computer’s hard.
HIPAA Compliance is an ongoing process. As regulations and technologies change you need to ensure your systems are secure and that your patience can trust you with their confidential data.
Our experts at Corsica Technologies can help you on your journey to HIPAA compliance as well as other cybersecurity concerns. Contact us today to schedule a HIPAA Consultation with our team

Ross Filipek
Ross is the CISO at Corsica Technologies. He has achieved CCIE Security and CISSP certifications, an MBA from the University of Notre Dame, and has 20 years of experience in the fields of computer and network security engineering and consulting. Ross provides virtual CISO services for clients and helps them to identify information security risks and implement administrative, procedural, and technical controls to mitigate. He works effectively with both technical and managerial personnel and is a trusted resource for our clients.






